A highly persistent threat (APT) group located in China called TheWizards is linked to a lateral movement tool called Spellbinder, which can promote middle (AITM) attacks.
“The spellbinder allows intermediate (AITM) attacks via IPv6 stateless address AutoconFiguration (SLAAC) spoofing, allowing it to travel sideways on compromised networks, intercept packets, redirect legal Chinese software traffic, and allow attackers to download malicious updates from servers that Mr. under said.”
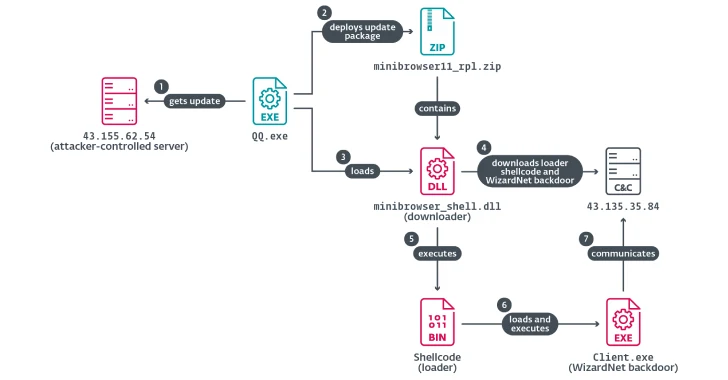
This attack paves the way for malicious downloaders delivered by hijacking the software update mechanism associated with Sogou Pinyin. The downloader then acts as a conduit for dropping a wizard net called a modular backdoor code name.
This is not the first time a Chinese threat actor has abused the software update process for Sogou Pinyin to provide its own malware. In January 2024, ESET detailed a hacking group called Blackwood that deployed an implant named NSPX30 by leveraging the update mechanism of Chinese input method software applications.

Then earlier this year, Slovak cybersecurity company revealed another threat cluster known as Plushdaemon, which utilized the same technique to distribute custom downloaders called Littledaemon.
The Wizards APT is known to target both individuals and gambling sectors in Cambodia, Hong Kong, mainland China, the Philippines and the United Arab Emirates.
It suggests that the Spellbinder IPv6 AITM tool has been used by threat actors since at least 2022. The exact initial access vector used in the attack is unknown at this stage, but the delivery of a ZIP archive containing four different files continues.
Threat parties will install “winpcap.exe” and run “avgaapplicationframehost.exe”. The DLL file then reads the shellcode from “log.dat”, runs it in memory, and launches the spellbinder in the process.

“Spellbinder uses the WinPCap library to capture packets and respond to packets when necessary,” explained Muñoz. “We can use IPv6’s Network Discovery Protocol to advertise the presence of IPv6-enabled routers in our network, and we are recruiting hosts or IPv6-enabled routers, so we can employ advertising devices as debt notifications.”
In one attack case observed in 2024, the threat actors are said to have used this method to provide a Trojanized version that provides a Trojanned Net that hijacks the Tencent QQ software update process at the DNS level to deliver a Trojanned Net that deploys equipped modular backdoors to receive and run .NET payloads in infected hosts.
Spellbinder turns this off by intercepting DNS queries for software update domains (“update.browser.qq[.]Issuing a DNS response using the IP address of the attacker control server (” 43.155.62[.]54″) Hosting malicious updates.

Another notable tool for TheWizards ‘Arsenal is Darknights. This is due to another Chinese hacking group, also known as Darknimbus by Trend Micro, which was tracked as Earth Minotaur. That being said, both clusters are treated as independent operators, citing differences in tools, infrastructure, and targeting footprints.
Since then, Sichuan Dianke Network Security Technology Co., Ltd. It has been revealed that a contractor from China’s Ministry of Public Safety, known as UPSEC, is a supplier of Darknimbus Malware.
“TheWizards uses a backdoor for Windows (WizardNet), but the hijacking server is configured to provide a Dark Knight for updates to applications running on Android devices,” says Muñoz. “This shows that Dianke Network Security is a digital quartermaster for TheWizards APT group.”
Source link