Threat Hunters is warning of a sophisticated web skimmer campaign that leverages legacy application programming interfaces (APIs) from payment processor stripes to validate payment information stolen before removal.
“This tactic ensures that only valid card data is sent to the attacker, making detection of operations more efficient and potentially difficult,” said Jscrambler researchers Pedroforna, David Alvez and Pedro Marcio in the report.
It is estimated that as many as 49 merchants have been affected by previous campaigns. Fifteen of the compromised sites have taken steps to remove malicious script injections. This activity has been rated as ongoing since at least August 20, 2024.

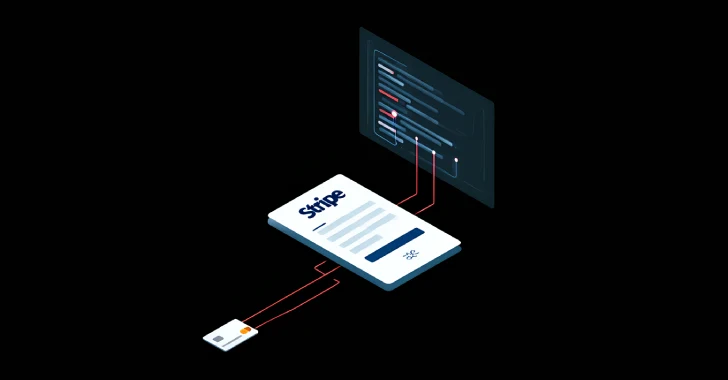
The campaign details were first flagged by security company source defense towards the end of February 2025, with web skimmers detailing the use of API.Stripe[.]com/v1/sources “API. This allows the application to accept a variety of payment methods. The endpoint has since been deprecated in favor of the new payment methods API.
Attack chain employs a malicious domain as the initial distribution point for JavaScript skimmers designed to intercept and hide legitimate payment forms on the order checkout page, provide replicas of legitimate striped payment screens, verify using the source API, and send them to remote servers in base 64 encoding format.
Jscrambler said that the threat actors behind the surgery are likely to be embedding early-stage scripts by leveraging vulnerabilities and misconceptions in WooCommerce, WordPress and Prestashop. This loader script helps you decrypt and launch the Base64 encoded next stage. This includes a URL pointing to a skimmer.
“The skimming script overlays a legitimate striped iframe with malicious ones designed to hide and mimic the appearance of it,” the researchers said. “Also, clone the ‘Order’ button and hide the real button. ”

Once the details are drawn, the user will receive an error message and ask you to reload the page. There is some evidence that suggests that the final skimmer payload is generated using some tool, as the script appears to be tailored to each target site.
The security company also discovered a skimmer script impersonating Square’s payment form, suggesting that it is likely that threat actors are targeting several payment service providers. And that’s not all. Skimming codes have also been observed to use cryptocurrencies such as Bitcoin, Ether (Ethereum), Tether and Litecoin to add other payment options.
“This sophisticated web skimming campaign highlights the evolving tactics used by attackers to keep them undetected,” the researchers said. “And as a bonus, they effectively exclude invalid credit card data and ensure that only valid credentials have been stolen.”
Source link