High-level government agencies in Sri Lanka, Bangladesh and Pakistan have emerged as targets for new campaigns organized by threat actors known as Sidewinders.
“The attackers used spear phishing emails paired with geophishing payloads to ensure that only victims of certain countries received malicious content,” Acronis researchers Santiago Pontiloli, Josse F Jegeny and Prakas Zavendaran said in a report shared with Hacker News.
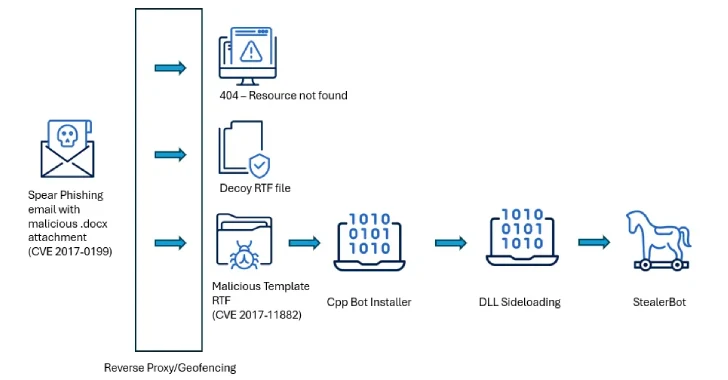
The attack chain utilizes spearfishing laiders as a starting point for activating the infection process and deploying known malware called Stealerbot. It is worth pointing out that this trick coincides with the recent sidewinder attack documented by Kaspersky in March 2025.

Part of the campaign’s goals, Acronis includes Bangladesh’s Telecommunications Regulatory Commission, the Ministry of Defense and the Ministry of Finance. Pakistan’s Indigenous Peoples’ Technology Development Bureau. Ministry of External Resources, Ministry of Finance, Ministry of Defense, and Central Bank of Sri Lanka.
The attack is characterized by the use of years of remote code execution flaws in Microsoft Office (CVE-2017-0199 and CVE-2017-11882) as an initial vector for deploying malware that can maintain permanent access in the South Asian government environment.

When the malicious document opens, triggers an exploit for CVE-2017-0199 to provide the next stage payload responsible for installing StealerBot using DLL sideload technology.
One notable tactic that Sidewinder employs is to ensure that spear phishing emails are linked to the Geofykend payload to ensure that only victims who meet targeting criteria are served to malicious content. If the victim’s IP address does not match, the empty RTF file will be sent as a decoy.
The malicious payload is an RTF file that weaponizes CVE-2017-11882, a memory corruption vulnerability in the equation editor, launches a shellcode-based loader that runs the Stealerbot malware.

According to Kaspersky, Stealerbot is a .NET implant designed to drop additional malware, launch a reverse shell, and collect a wide range of data from compromised hosts such as screenshots, keystrokes, passwords, files, and more.
“Sidewinder has maintained a stable pace of operation without long-term inactivity, maintaining patterns that reflect organizational continuity and sustained intentions, demonstrating consistent activity over time,” the researchers said.
“A closer analysis of tactics, techniques, and procedures (TTPS) reveals high levels of control and accuracy, delivering malicious payloads only to carefully selected targets, often providing only a limited amount of time.”
Source link