Asus has released an update to address two security flaws affecting Asus Driverhub. This could allow attackers to leverage software to enable remote code execution.
DriverHub is a tool designed to automatically detect your computer’s motherboard model and display driver updates required for subsequent installations by communicating with a dedicated site hosted on “Driverhub.asus”.[.]com. “
The defects identified in the software are listed below –
CVE-2025-3462 (CVSS score: 8.4) – Origin validation error vulnerability that could allow an incorrect source to interact with software features via created HTTP requests CVE-2025-3463 (CVSS score: 9.4) – Possible to enable an inappropriate certificate validation vulnerability.
Security researcher Mrbruh has been admitted to discovering and reporting two vulnerabilities, which could be exploited to achieve remote code execution as part of a one-click attack.

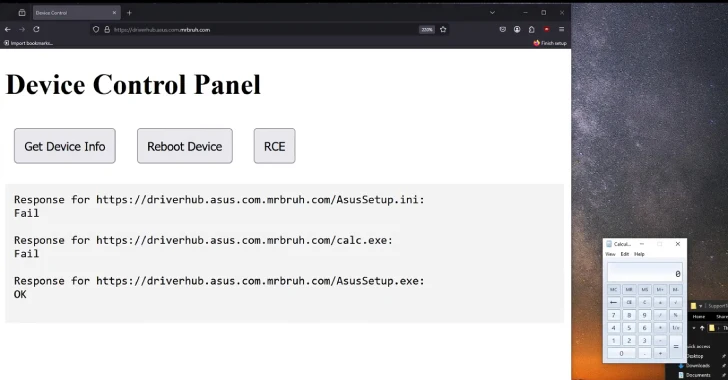
The attack chain involves tricking users to visit subdomains of Driverhub.asus essentially unsuspecting.[.]com (e.g. driverhub.asus.com..com), then leverages driverhub’s updateapp endpoint to run a legitimate version of the “asussetup.exe” binary with options configured to run files hosted in fake domains.
“When you run asussetup.exe, it first reads from asussetup.ini, which contains metadata about the driver,” the researchers explained in the technical report.
“When you run asussetup.exe with the -s flag (Driverhub uses this to do a silent install), it runs everything specified in SilentInstallrun. In this case, the INI file specifies a CMD script that performs an automatic headless installation of the driver, but you can run anything.”
What attackers need to successfully separate their exploits is to create a domain and host three files, a malicious payload.
Following the responsible disclosure on April 8, 2025, this issue was fixed by ASUS on May 9. There is no evidence that vulnerability has been exploited in the wild.
“This update includes important security updates and ASUS strongly encourages users to update their ASUS Driverhub installation to the latest version,” the company said in a bulletin. “For the latest software updates, open ASUS Driverhub and[今すぐ更新]You can access it by clicking the button. ”
Source link