Cybersecurity researchers have revealed a critical container escape vulnerability in the NVIDIA Container Toolkit.
The vulnerability tracked as CVE-2025-23266 has a CVSS score of 9.0 out of 10.0. It is codenamed nvidiascape by Cloud Security Company Wiz, owned by Google.
“The NVIDIA Container Toolkit for all platforms contains vulnerabilities in some hooks used to initialize containers. Attackers can increase their permissions and execute arbitrary code,” Nvidia said in their bug advisory.

“Successful use of this vulnerability could lead to privilege escalation, data tampering, information disclosure, and denial of service.”
This drawback affects NVIDIA GPU operators with 25.3.0 on all versions of the NVIDIA Container Toolkit up to 1.17.7 and NVIDIA GPU operators. GPU manufacturers deal with versions 1.17.8 and 25.3.1, respectively.
The NVIDIA Container Toolkit refers to a collection of libraries and utilities that allow users to build and run GPU-accelerated Docker containers. The NVIDIA GPU operator is designed to automatically deploy these containers to GPU nodes in a Kubernetes cluster.
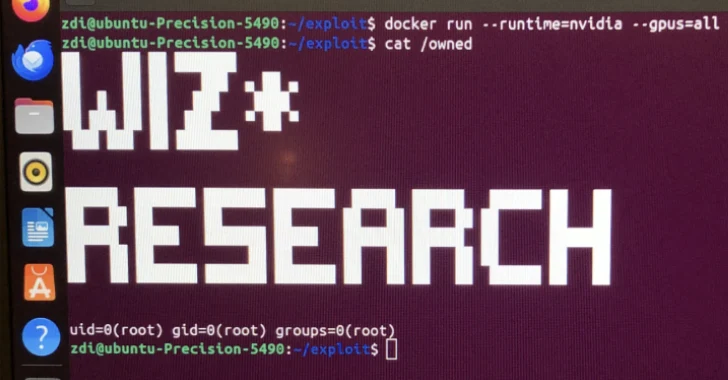
Shared details of the flaw in Thursday’s analysis, Wiz said the drawback would affect 37% of the cloud environment, allowing attackers to access, steal or manipulate sensitive data and their own models from all other customers running on the same shared hardware through three lines of exploit.
The vulnerability is attributed to a misconception about how the toolkit handles the Open Container Initiative (OCI) Hook “CreateContainer”. A successful exploit for CVE-2025-23266 could result in a complete acquisition of the server. Wiz also characterized the flaw as “incredibly” easy to weaponize.
“By setting LD_PRELOAD to DockerFile, attackers can instruct NVIDIA-CTK hooks to load malicious libraries,” added Wiz researchers Nir Ohfeld and Shir Tamari.
“What’s worse, CreateContainer Hook runs using a working directory set up in the container’s root file system. This means that malicious libraries can be loaded directly from the container image with a simple path and completed the exploit chain.”

All of this can be achieved with a “surprisingly simple 3-line dockerfly” that loads the attacker’s shared object file into the privileged process.
This disclosure came months after Wiz detailed another vulnerability bypass in the NVIDIA Container Toolkit (CVE-2024-0132, CVSS score: 9.0 and CVE-2025-23359, CVSS score: 8.3) to achieve a full host takeover.
“High hype about AI security risks tends to focus on AI-based futuristic attacks, but vulnerabilities in the ever-growing “old-school” infrastructure of the AI technology stack continue to be an immediate threat that security teams should prioritize,” Wiz said.
“Furthermore, this study emphasizes that containers should not rely on as the only means of isolation, rather than as a strong security barrier. Especially when designing applications in multi-tenant environments, it is always necessary to implement at least one strong isolation barrier, such as virtualization, “assuming vulnerabilities.” ”
Source link