On Friday, Amazon said it had flagged and confused what it described as an opportunistic waterhole campaign organized by the Russian-linked APT29 actor as part of its intelligence gathering efforts.
The campaign is “designed to use compromised websites to redirect visitors to malicious infrastructure, and trick users into approving attacker-controlled devices via Microsoft’s device code authentication flow,” said CJ Moses, Amazon’s Chief Information Security Officer.
APT29 is a name assigned to a country sponsored hacking group that has been tracked as Bluebravo, Cloked Ursa, Cozylarch, Cozy Bear, Earth Koshchei, Icecap, Midnight Blizzard, and The Dukes, and is a country-sponsored hacking group with ties to Russian Foreign Information Services (SVR).

Over the past few months, prolific threat actors have been linked to attacks that leverage malicious Remote Desktop Protocol (RDP) configuration files to target Ukrainian entities and remove sensitive data.
Since the beginning of the year, it has been observed that hostile groups will employ a variety of phishing methods, including device code phishing and device-participating phishing to gain unauthorized access to Microsoft 365 accounts.
Recently in June 2025, Google said it had observed a threat cluster that APT29 partnered with APT29 to weaponize Google account features called application-specific passwords to allow access to victims’ emails. The highly targeted campaign was attributed to UNC6293.
The latest activities identified by Amazon’s Threat Intelligence Team highlight threat actors’ continued efforts to harvest qualifications and collect intelligence of interest, while simultaneously reducing commerce.
“This opportunistic approach demonstrates the continuous evolution of APT29, expanding its operations and gaining a wider net in its intelligence gathering efforts,” Moses said.
The attack was injected with JavaScript, where APT29 compromised various legitimate websites and redirected around 10% of visitors to the actor control domain.[.]com, mimics its cloudflare verification page and gives the illusion of legitimacy.

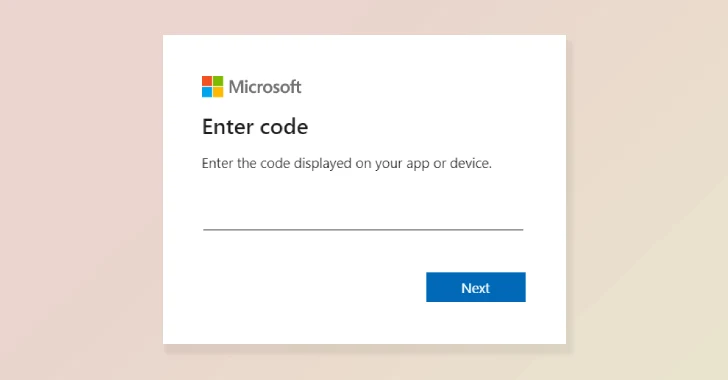
In reality, the ultimate goal of the campaign was to tempt victims to enter legitimate device codes generated by threat actors on the sign-in page, effectively allowing access to Microsoft accounts and data. This technique was detailed in February 2025 by both Microsoft and Volexity.
This activity is also worth noting that it incorporates a variety of evasion techniques, such as Base64 encoding to hide malicious code, setting cookies to prevent repeated redirects of the same visitors, and moving to new infrastructure when blocked.
“Our team continued to track and disrupt operations despite the actors’ attempts to migrate to new infrastructure, including moving from AWS to another cloud provider,” Moses said. “After the intervention, we observed that actors register additional domains such as cloudflare.redirectpartners.[.]com tried to lure the victim into the Microsoft Device Code authentication workflow. ”
Source link