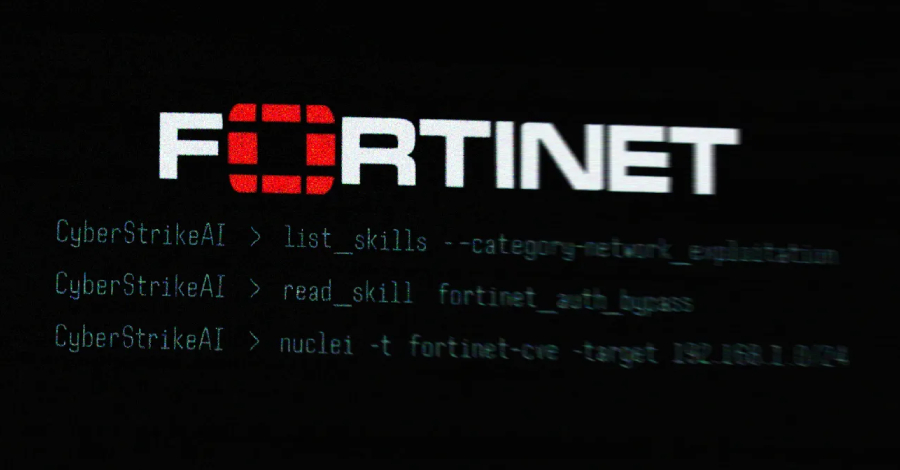
The attackers behind the recently revealed artificial intelligence (AI)-assisted campaign targeting Fortinet’s FortiGate appliances leveraged an open-source AI-native security testing platform called CyberStrikeAI to carry out the attack.
This new discovery is attributed to Team Cymru, whose use was detected after analyzing the IP address (‘212.11.64’).[.]250″) was used by a suspected Russian-speaking attacker to perform automated mass scans of vulnerable appliances.
CyberStrikeAI is “an open source artificial intelligence (AI) offensive security tool (OST) developed by a developer based in China that we believe has some connection to the Chinese government,” said security researcher Will Thomas (also known as @BushidoToken).
Details of the AI-powered activity were revealed last month when Amazon Threat Intelligence announced that it detected an unknown attacker using generative artificial intelligence (AI) services such as Anthropic Claude and DeepSeek to systematically target FortiGate devices and compromise more than 600 appliances in 55 countries.
According to the GitHub repository description, CyberStrikeAI is built with Go and integrates over 100 security tools to enable vulnerability discovery, attack chain analysis, knowledge capture, and results visualization. It is maintained by a Chinese developer with the online alias Ed1s0nZ.
Team Cymru announced that it observed 21 unique IP addresses running CyberStrikeAI on servers primarily hosted in China, Singapore, and Hong Kong between January 20 and February 26, 2026. Additional servers associated with this tool were also discovered in the United States, Japan, and Switzerland.
In addition to hosting CyberStrikeAI, the Ed1s0nZ account has exposed several other tools that show interest in exploiting and jailbreaking AI models.
Watermark-tool adds an invisible digital watermark to your documents. Banana_blackmail (Golang-based ransomware), PrivHunterAI (Golang-based tool that uses Kimi, DeepSeek, and GPT models to detect privilege escalation vulnerabilities). ChatGPTJailbreak. It includes a README.md file that contains prompts to jailbreak OpenAI ChatGPT by tricking it into entering Do Anything Now (DAN) mode or asking it to act as ChatGPT with developer mode enabled. InfiltrateX is a Golang-based scanner for detecting privilege escalation vulnerabilities. VigilantEye is a Golang-based tool that monitors the disclosure of sensitive information such as phone numbers and ID card numbers in a database. It is configured to send alerts via the WeChat Work bot if a potential data breach is detected.
“Additionally, Ed1s0nZ’s GitHub activity indicates that they are interacting with organizations that potentially support the Chinese government’s state-sponsored cyber operations,” Thomas said. “This includes private Chinese companies with known ties to China’s Ministry of State Security (MSS).”
One such company contacted by developers is Knownsec 404, a Chinese security vendor. The company suffered a major leak of more than 12,000 internal documents late last year, exposing a trove of stolen data including the company’s employee data, government customers, hacking tools, information related to South Korean phone records and Taiwanese critical infrastructure organizations, and the inner workings of ongoing cyber operations targeting other countries.

“On the surface, KnownSec appeared to be just a security company, but this is only a half-truth,” DomainTools said in an analysis published in January, describing it as a “state-aligned cyber contractor” capable of supporting China’s national security, intelligence, and military objectives.
“in fact, […] China has shadow organizations working for the People’s Liberation Army, the MSS, and the organs of the Chinese security state. This leak exposed a company operating far beyond the role of a typical cybersecurity vendor. Tools like ZoomEye and the Critical Infrastructure Target Library provide China with a global reconnaissance system that catalogs millions of foreign IPs, domains, and organizations mapped by sector, geography, and strategic value. ”
Ed1s0nZ was also observed to actively modify and remove references to the README.md file in the repository of the same name, which was awarded the China National Information Security Vulnerability Database (CNNVD) Level 2 Contribution Award. The developer also claims that “everything shared here is purely for research and learning.”
According to research published by Bitsight last month, China maintains two separate vulnerability databases: CNNVD and China National Vulnerability Database (CNVD). CNNVD is supervised by the Ministry of State Security, while CNVD is managed by CNCERT. Recorded Future’s previous findings revealed that CNNVD takes longer to publish vulnerabilities with higher CVSS scores than vulnerabilities with lower CVSS scores.
“The developer’s recent attempt to remove references to CNNVD from its GitHub profile indicates an active effort to hide these state connections, likely to protect the operational viability of the tool as it grows in popularity,” Thomas said. “CyberStrikeAI adoption is accelerating and represents an alarming evolution in the proliferation of AI-enhanced offensive security tools.”
Source link