Microsoft on Thursday revealed details of a wide-ranging new ClickFix social engineering campaign that leveraged the Windows Terminal app as a way to activate a sophisticated attack chain and deploy the Lumma Stealer malware.
This activity, identified in February 2026, allows users to install Windows[ファイル名を指定して実行]Instead of launching a dialog and instructing you to paste a command into it, a terminal emulator program is utilized.
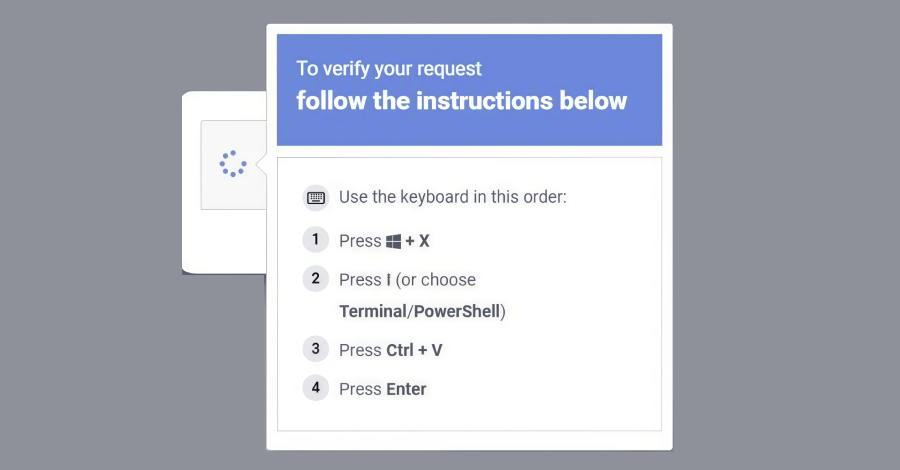
In a series of posts about X, the Microsoft Threat Intelligence team said, “The campaign instructs targets to directly launch Windows Terminal (wt.exe) using the Windows+X→I shortcut, directing users to a privileged command execution environment that blends into legitimate administrative workflows and appears more trustworthy to users.”
What’s notable about the latest variants is that they leverage the legitimacy of Windows Terminal to evade detections specifically designed to flag run dialog abuse, not to mention trick unsuspecting users into executing malicious commands delivered via fake CAPTCHA pages, troubleshooting prompts, or other forms of validation enticement.
The post-breach attack chain is also unique. When a user pastes a hex-encoded, XOR-compressed command copied from the ClickFix lure page into a Windows Terminal session, it spans additional terminal/PowerShell instances and ultimately calls a PowerShell process responsible for decoding the script.
This downloads a ZIP payload and a legitimate but renamed 7-Zip binary, the latter being saved to disk with a random filename. The utility then begins extracting the contents of the ZIP file, triggering a multi-step attack chain that includes the following steps:
Obtain more payloads Configure persistence through scheduled tasks Configure Microsoft Defender exclusions Extract machine and network data Deploy Lumma Stealer using a technique called QueueUserAPC() by injecting malware into the “chrome.exe” and “msedge.exe” processes
“This stealer targets high-value browser artifacts such as web data and login data, harvesting stored credentials, and exfiltrating them to attacker-controlled infrastructure,” Microsoft said.
The Windows maker said it also detected a second attack vector. As part of this, when the compressed command is pasted into the Windows Terminal, a randomly named batch script is downloaded to the “AppData\Local” folder using “cmd.exe”, and a Visual Basic script is written to the Temp folder (aka %TEMP%).
“The batch script is then executed via cmd.exe with the /launched command line argument. The same batch script is then executed via MSBuild.exe, resulting in LOLBin exploitation,” the report added. “The script connects to a Crypto Blockchain RPC endpoint, demonstrating ether hiding techniques, and performs QueueUserAPC()-based code injection into the chrome.exe and msedge.exe processes to collect web and login data.”
Source link