Cybersecurity researchers have revealed details of a new Linux backdoor named PamDOORa that is being advertised on the Rehub Russian cybercrime forum for $1,600 by a threat actor called “darkworm.”
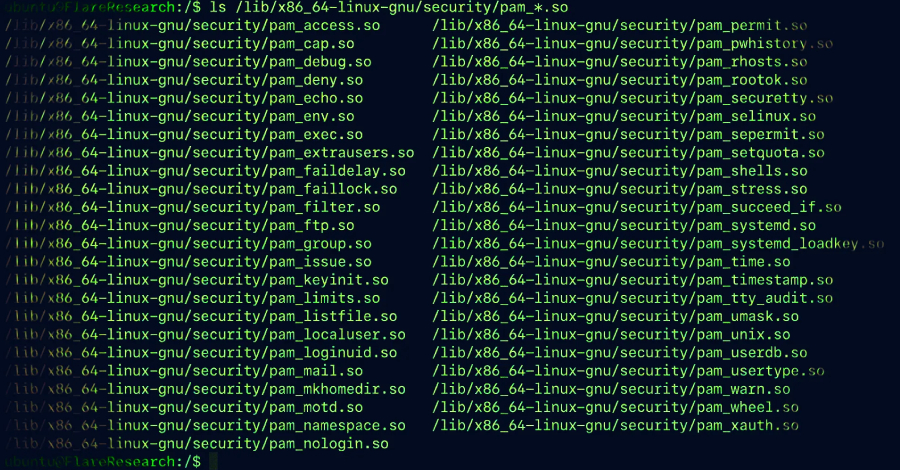
The backdoor is designed as a Pluggable Authentication Module (PAM)-based post-exploitation toolkit that allows persistent SSH access through a combination of a magic password and a specific TCP port. It can also collect credentials from all legitimate users who authenticate through a compromised system.
“The tool, called PamDOORa, is a new PAM-based backdoor designed to act as a post-exploitation backdoor, allowing authentication to the server via OpenSSH,” Flare.io researcher Assaf Morag said in a technical report. “This is said to be persistent on Linux systems (x86_64).”
PamDOORa is the second Linux backdoor after Plague to target the PAM stack. PAM is a security framework for Unix/Linux operating systems that allows system administrators to use pluggable modules to incorporate multiple authentication mechanisms into existing systems or update them (for example, switching from passwords to biometrics) without having to rewrite existing applications.
Because PAM modules typically run with root privileges, a compromised, misconfigured, or malicious module can pose a significant security risk and open the door to credential harvesting and unauthorized access.
“Despite its strengths, the modular nature of the Pluggable Authentication Module (PAM) poses risks. In particular, since PAM does not store passwords and transmits values in clear text, malicious modifications to the PAM module could create backdoors or steal user credentials,” Group-IB noted in September 2024.
“The pam_exec module, which allows the execution of external commands, could be exploited by attackers to gain unauthorized access or establish persistent control by injecting malicious scripts into PAM configuration files.”

The Singaporean security vendor also detailed how to manipulate PAM settings for SSH authentication to run scripts via pam_exec. This effectively allows a malicious attacker to obtain a privileged shell on the host and facilitate stealth persistence.
According to Flare.io’s latest findings, PamDOORa not only enables credential theft, but also incorporates anti-forensic features that systematically alter authentication logs to erase any trace of malicious activity.
Although there is no evidence that this malware has been used in real-world attacks, the infection chain for distributing the malware likely involves the attacker first gaining root access to the host through other means, deploying the PamDOORa PAM module to obtain credentials, and establishing persistent access via SSH.
The initial asking price on March 17, 2026 was $1,600, but the “Dark Worm” persona has since lowered the price by almost 50% to $900 as of April 9, indicating either a lack of buyer interest or an intention to accelerate the sale.

“PamDOORa represents an evolution of existing open source PAM backdoors,” Morag explained. “While the individual techniques (PAM hooks, credential capture, log tampering) are well documented, their integration into a unified, modular implant with debug protection, network-enabled triggers, and builder pipelines brings them closer to operator-level tools than the crude proof-of-concept scripts found in most public repositories.”
Source link