Checkmarx has confirmed that a fixed version of the Jenkins AST plugin has been published on the Jenkins Marketplace.
“If you are using the Checkmarx Jenkins AST plugin, you should ensure that you are using version 2.0.13-829.vc72453fa_1c16 published on or before December 17, 2025,” the cybersecurity firm said in a statement over the weekend.
As of this writing, Checkmarx has released 2.0.13-848.v76e89de8a_053 on both GitHub and Jenkins Marketplace, but its incident update still states “A new version of this plugin is in the works.” It did not say how the malicious plugin version was made public.
This development is the latest attack orchestrated by TeamPCP targeting Checkmarx. The incident comes weeks after the notorious cybercriminal group was believed to have compromised a KICS Docker image, two VS Code extensions, and a GitHub Actions workflow to push credential-stealing malware.
This breach briefly compromised the Bitwarden CLI npm package, which served as a similar stealer capable of collecting a wide range of developer secrets.
TeamPCP has been implicated in a series of breaches since March 2026 as part of a larger campaign to exploit the trust inherent in the software supply chain to spread malware and expand its reach.
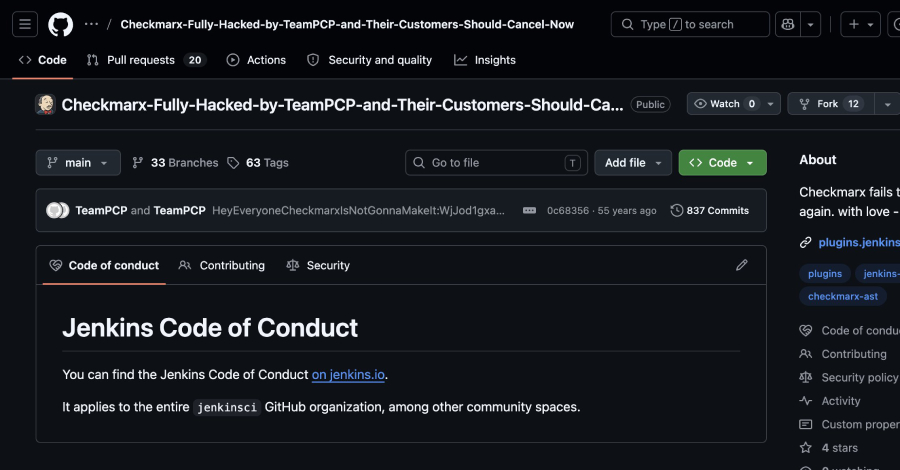
According to details shared by security researchers Adnan Khan and SOCRadar, TeamPCP allegedly compromised the plugin’s GitHub repository and changed its name to “Checkmarx-Fully-Hacked-by-TeamPCP-and-Their-Customers-Should-Cancel-Now.”
The compromised repository was also updated to include the following description: “Checkmarx once again failed to rotate secrets. With love – TeamPCP.”
“The fact that TeamPCP is back within the Checkmarx system after just a few weeks points to one of two possibilities: either the initial remediation was incomplete and credentials were not fully rotated, or the group may have maintained a foothold that was not identified in the March response,” SOCRadar said.
“The upcoming second Checkmarx incident suggests that this group is actively monitoring reentry points, testing the depth of past repairs and exploiting gaps.”
Source link