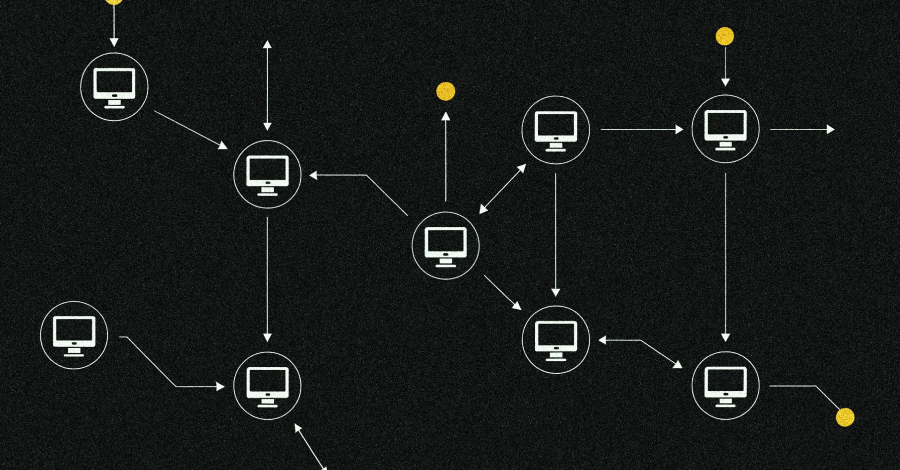
Cybersecurity researchers have revealed details of a new botnet loader called Aeternum C2. This botnet loader uses blockchain-based command and control (C2) infrastructure to make it more resilient to takedown efforts.
“Rather than relying on traditional servers or domains for command and control, Aeternum stores instructions on the public Polygon blockchain,” Qrator Labs said in a report shared with The Hacker News.
“This network is widely used in decentralized applications, including Polymarket, the world’s largest prediction market. This approach makes Aeternum’s C2 infrastructure effectively persistent and resistant to traditional deletion methods.”
This is not the first time a botnet relying on C2’s blockchain has been discovered. In 2021, Google announced that it had taken steps to disrupt a botnet known as Glupteba that uses the Bitcoin blockchain as a backup C2 mechanism to obtain real C2 server addresses.
Details of Aeternum C2 first emerged in December 2025, when Outpost24’s KrakenLabs revealed that a threat actor named LenAI was promoting the malware on underground forums for $200, which gave customers access to the panel and configured builds. For $4,000, customers were allegedly promised the entire C++ codebase and updates.
The malware works by writing commands issued to infected hosts into smart contracts on the Polygon blockchain, with a native C++ loader available in both x32 and x64 builds. The bot then queries a public remote procedure call (RPC) endpoint to read these commands.
All of this is managed through a web-based panel from which customers can select a smart contract, choose a command type, specify a payload URL, and update it. This command can target all endpoints or specific endpoints, and after being written to the blockchain as a transaction, it will be available to all compromised devices polling the network.
“Once a command is confirmed, it cannot be modified or deleted by anyone other than the wallet owner,” Qrator Labs said. “Operators can manage multiple smart contracts simultaneously, each potentially offering different payloads and functionality such as clippers, stealers, RATs, and miners.”
According to a two-part study published by Ctrl Alt Intel earlier this month, the C2 Panel is implemented as a Next.js web application and will allow operators to deploy smart contracts on the Polygon blockchain. The smart contract contains a function that, when called by the malware via Polygon RPC, returns an encrypted command that is then decoded and executed on the victim’s machine.

The malware not only leverages blockchain to turn it into a takedown-resistant botnet, but also packs in a variety of anti-analysis features to extend the lifespan of the infection. This includes checks to detect virtualized environments in addition to giving customers the ability to scan builds via Kleenscan to ensure they have not been flagged by antivirus vendors.
“The operating costs are negligible: $1 worth of MATIC, the native token of the Polygon network, is enough for 100 to 150 command transactions,” the Czech cybersecurity vendor said. “Operators do not need to rent servers, register domains, or maintain any infrastructure other than a local copy of a cryptocurrency wallet or panel.”
The threat actor then attempted to sell the entire toolkit for an asking price of $10,000, claiming that they lacked support time and were involved in another project. “I will sell the entire project to one person with all ‘rights’ and permission for resale and commercial use,” LenAI said. “It also provides helpful development tips and notes that you may not have been able to implement due to lack of time.”
It’s worth noting that LenAI is also behind a second crimeware solution called ErrTraffic. This solution allows threat actors to automate ClickFix attacks by generating fake glitches on compromised websites to induce a false sense of urgency and trick users into following malicious instructions.
The disclosure comes after Infrawatch published details of an underground service that deploys specialized laptop hardware into U.S. homes and integrates the devices into a residential proxy network called DSLRoot, which redirects malicious traffic.
This hardware is designed to run a Delphi-based program called DSLPylon with the ability to enumerate supported modems on the network, and remotely control residential networking equipment and Android devices through Android Debug Bridge (ADB) integration.
“Attribution analysis revealed that the operator is a Belarusian citizen residing in Minsk and Moscow,” InfraWatch said. “DSLRoot is estimated to operate approximately 300 active hardware devices in more than 20 states in the United States.”

The operator has been identified as Andrei Holas (also known as Andre Holas and Andrei Golas), and the service is being advertised on BlackHatWorld by a user going by the alias GlobalSolutions, who claims to be selling physical residential ADSL proxies for $190 per month for unlimited access. A six-month subscription is available for $990, and an annual subscription is available for $1,750.
“DSLRoot’s custom software provides automatic remote management of consumer modems (ARRIS/Motorola, Belkin, D-Link, ASUS) and Android devices via ADB, enabling IP address rotation and connection control,” the company said. “The network operates without authentication, allowing clients to anonymously route traffic through US residential IPs.”
Source link