The suspected China-based cyber espionage operation has targeted military organizations in Southeast Asia as part of a state-sponsored campaign dating back to at least 2020.
Palo Alto Networks Unit 42 is tracking threat activity under the designation CL-STA-1087. CL refers to clusters and STA stands for state-backed motives.
Security researchers Lior Rochberger and Yoav Zema said: “This operation demonstrated strategic patience and a focus on highly targeted intelligence gathering rather than mass data theft.” “The attackers behind this cluster actively searched for and collected very specific files regarding military capabilities, organizational structure, and collaborative activities with Western forces.”
This campaign exhibits characteristics commonly associated with advanced persistent threat (APT) operations, including carefully crafted delivery methods, defensive evasion strategies, a highly stable operational infrastructure, and custom payload deployment designed to support continued unauthorized access to compromised systems.
Tools used by threat actors in their malicious activities include backdoors named AppleChris and MemFun, and a credential harvester named Getpass.
The cybersecurity vendor said it detected the intrusion set after identifying a suspicious PowerShell execution, which caused the script to sleep for six hours, after which it could create a reverse shell to a command-and-control (C2) server controlled by a threat actor. The exact initial access vector used in the attack remains unknown.
The infection sequence includes the deployment of AppleChris. Various versions of AppleChris are dropped across targeted endpoints following lateral movement to maintain persistence and evade signature-based detection. Threat actors have also been observed conducting searches related to official meeting records, joint military operations, and detailed assessments of operational capabilities.
“The attackers were particularly interested in files related to military organizational structure and strategy, including command, control, communications, computers, and information (C4I) systems,” the researchers said.
Both AppleChris variants and MemFun are designed to access shared Pastebin accounts, acting as dead drop resolvers that retrieve the actual C2 address stored in Base64 decoded format. One version of AppleChris relies on Dropbox to extract C2 information using a Pastebin-based approach as a fallback option. Pastebin Paste dates back to September 2020.
Launched by the DLL hijack, AppleChris initiates a connection with the C2 server and receives commands that allow it to enumerate drives, list directories, upload/download/delete files, enumerate processes, run remote shells, and create silent processes.
The second tunneler variant represents an evolution of the previous version by using only Pastebin to obtain the C2 address, in addition to introducing advanced network proxy features.
“To evade automated security systems, some malware variants employ sandbox evasion tactics during execution,” Unit 42 said. “These variants trigger delayed execution through sleep timers of 30 seconds (EXE) and 120 seconds (DLL), effectively exceeding the typical monitoring window of automated sandboxes.”
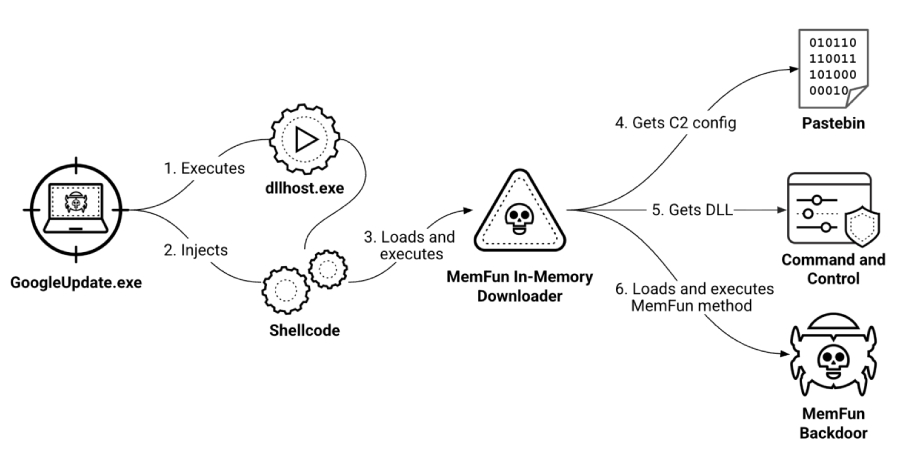
MemFun is launched through a multi-stage chain. The initial loader injects shellcode that is responsible for launching the in-memory downloader. Its main purpose is to retrieve the C2 configuration details from Pastebin, and retrieve the DLL that communicates with the C2 server and triggers the execution of the backdoor.
The DLL is retrieved from the C2 at runtime, making it easy for an attacker to deliver other payloads without changing anything. This behavior turns MemFun into a modular malware platform rather than a static backdoor like AppleChris.
MemFun execution begins with a dropper that performs anti-forensic checks before changing its own file creation timestamps to match the creation times of Windows system directories. It then uses a technique known as process helloing to inject its main payload into the memory of the suspended process associated with ‘dllhost.exe’.
In doing so, the malware masquerades as a legitimate Windows process to avoid flying under the radar and leaving additional artifacts on disk.
A custom version of Mimikatz known as Getpass is also used in the attack to attempt to escalate privileges and extract plaintext passwords, NTLM hashes, and authentication data directly from the “lsass.exe” process memory.
“The attackers behind the cluster demonstrated operational fortitude and security awareness,” Unit 42 concluded. “They maintained dormant access for several months while focusing on precision intelligence gathering and implementing robust operational security measures to ensure the longevity of the campaign.”
Source link