New findings from Kaspersky Lab show that the recently discovered kernel exploits for two security vulnerabilities used in the Apple iOS exploit kit Coruna are updated versions of the same exploits used in the 2023 Operation Triangulation campaign.
“When Coruna was first reported, the publicly available evidence was not enough to link its code to Triangulation. Shared vulnerabilities alone cannot prove shared authorship,” Boris Larin, principal security researcher at Kaspersky GReAT, told The Hacker News in a statement.
“Coruna is not a patchwork of public exploits; it is a continual maintenance and evolution of the original Operation Triangulation framework. The inclusion of checks for recent processors such as M3 and newer iOS builds indicates that the original developers have actively extended this codebase. What began as a precision spy tool is now being deployed indiscriminately.”
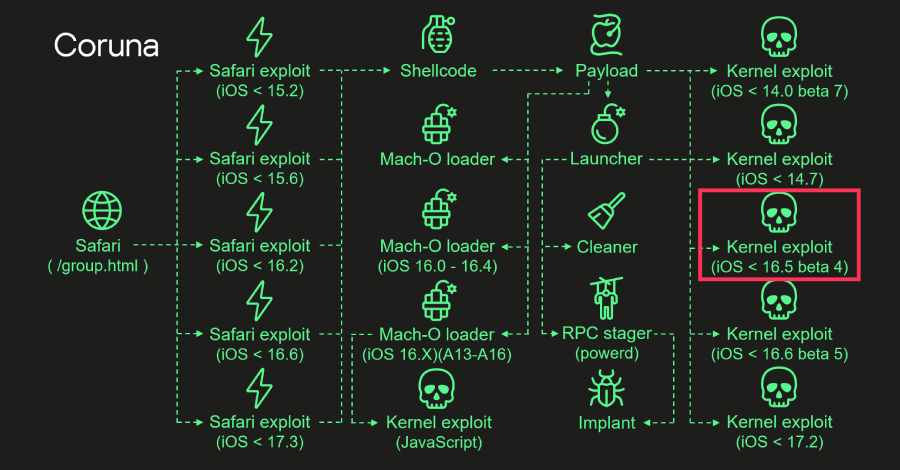
Coruna was first documented by Google and iVerify earlier this month as targeting Apple iPhone models running iOS versions 13.0 to 17.2.1.
The kit was first used by an anonymous monitoring company customer early last year, but has since been leveraged by nation-state attackers believed to be affiliated with Russia in a watering hole attack in Ukraine and a large-scale exploitation campaign that leveraged a cluster of fake Chinese gambling and cryptocurrency websites to deliver data-stealing malware known as PlasmaLoader (also known as PLASMAGRID).
This exploit kit contains 5 complete iOS exploit chains and a total of 23 exploits, including CVE-2023-32434 and CVE-2023-38606. Both were first used as zero-days in Operation Triangulation, a sophisticated campaign targeting iOS devices that involved the exploitation of four vulnerabilities in Apple’s mobile operating system.
Kaspersky’s latest findings show that both Triangulation and Coruna kernel exploits were created by the same author, and that Coruna also uses four additional kernel exploits. The Russian security vendor said these exploits are all built on the same kernel exploit framework and share common code.
Specifically, the code includes support for Apple’s A17, M3, M3 Pro, and M3 Max processors, as well as checks for iOS 17.2 and iOS version 16.5 Beta 4, with the latter patching all four vulnerabilities exploited as part of Operation Triangulation. Meanwhile, the iOS 17.2 check is aimed at taking into account newer exploits, Kaspersky said.
The starting point for the attack is when a user visits a compromised website in Safari, the stager fingerprints the browser and serves the appropriate exploit based on the browser and operating system version. This paves the way for execution of the payload that triggers the kernel exploit.
“After downloading the necessary components, the payload begins executing the kernel exploit, Mach-O loader, and malware launcher,” Kaspersky said. “The payload selects the appropriate Mach-O loader based on firmware version, CPU, and presence of iokit-open-service privileges.”
The launcher is the primary orchestrator responsible for initiating post-exploitation activities, leveraging kernel exploits to drop and execute the final implant. It also cleans up artifacts that have been exploited to hide forensic traces.
“Originally developed for cyber espionage purposes, this framework is now being used by a broader class of cyber criminals, putting millions of users with unpatched devices at risk,” Larin said. “Given its modular design and ease of reuse, we expect other threat actors to incorporate it into their attacks.”
The development comes after a new version of the iPhone exploit kit DarkSword was leaked on GitHub, raising concerns that it could equip more attackers with advanced capabilities to compromise devices, effectively turning what was once an elite hacking tool into a mass exploitation framework. The release of the new version was first reported by TechCrunch.
Source link