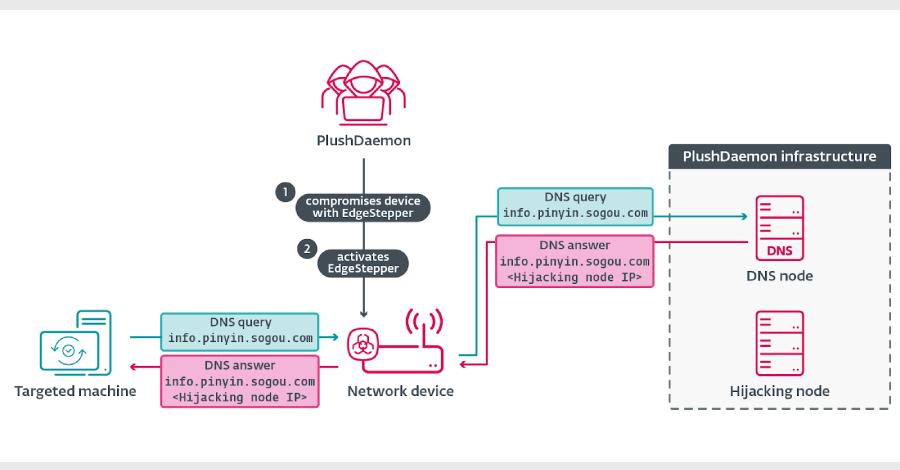
A threat actor known as PlushDaemon has been observed using a previously undocumented Go-based network backdoor (codenamed EdgeStepper) to facilitate adversary-man-in-the-middle (AitM) attacks.
EdgeStepper “redirects all DNS queries to an external malicious hijacking node, effectively rerouting traffic from legitimate infrastructure used for software updates to attacker-controlled infrastructure,” ESET security researcher Facundo Muñoz said in a report shared with Hacker News.
PlushDaemon is known to have been active since at least 2018 and is assessed to be a China-aligned group that has attacked organizations in the United States, New Zealand, Cambodia, Hong Kong, Taiwan, South Korea, and mainland China.

The information was first documented in early January by a Slovak cybersecurity firm detailing a supply chain attack by a South Korean virtual private network (VPN) provider called IPany that targeted a South Korean semiconductor company and an unidentified software developer using a feature-rich implant called SlowStepper.
Among the attackers’ victims are a university in Beijing, a Taiwanese company manufacturing electronics, a company in the automotive sector, and a branch of a Japanese company in the manufacturing sector. ESET announced earlier this month that it observed PlushDaemon targeting two companies with SlowStepper this year: a company in the automotive sector in Cambodia and a branch of a Japanese company in the manufacturing sector.

The primary initial access mechanism for threat actors is to leverage AitM poisoning. This technique has been adopted by a growing number of China-related Advanced Persistent Threat (APT) clusters over the past two years, including LuoYu and Evasive.
Panda, BlackTech, TheWizards APT, Blackwood, Font Goblin. ESET said it is tracking 10 active groups linked to China that have hijacked software update mechanisms for initial access and lateral movement.
This attack essentially begins with an attacker compromising an edge network device (such as a router) that the target may connect to. This is done by exploiting security flaws in the software or via weak credentials to enable deployment of caEdgeStepper.
“EdgeStepper then begins redirecting DNS queries to the malicious DNS node, verifies whether the domain in the DNS query message is related to the software update, and if so, replies with the IP address of the hijacking node,” Muñoz explained. “Alternatively, we have observed that some servers are both DNS nodes and hijack nodes, in which case the DNS node responds to DNS queries with its own IP address.”

Internally, the malware consists of two moving parts. Distributor module that resolves IP addresses associated with the DNS node domain (‘test.dsc.wcsset’).[.]com”) to call the Ruler component, which uses iptables to configure IP packet filter rules.
In this attack, EdgeStepper hijacks the update channels of several Chinese software, including Sogou Pinyin, and specifically checks for delivery of a malicious DLL (‘popup_4.2.0.2246.dll’, also known as LittleDaemon) from threat actor-controlled servers. The first stage, LittleDaemon, deployed via a hijacked update, is designed to communicate with the attacker node to obtain a downloader called DaemonicLogistics if SlowStepper is not running on the infected system.
The main purpose of DaemonicLogistics is to download and execute the SlowStepper backdoor from the server. SlowStepper supports an extensive feature set to collect system information, files, browser credentials, extract data from numerous messaging apps, and even uninstall itself.
“These implants give PlushDaemon the ability to compromise targets anywhere in the world,” Muñoz said.
Source link