Last week, the FBI seized and removed two websites associated with the pro-Iranian hacktivist group Handara, which claimed responsibility for the devastating cyberattack on U.S. medical technology giant Stryker.
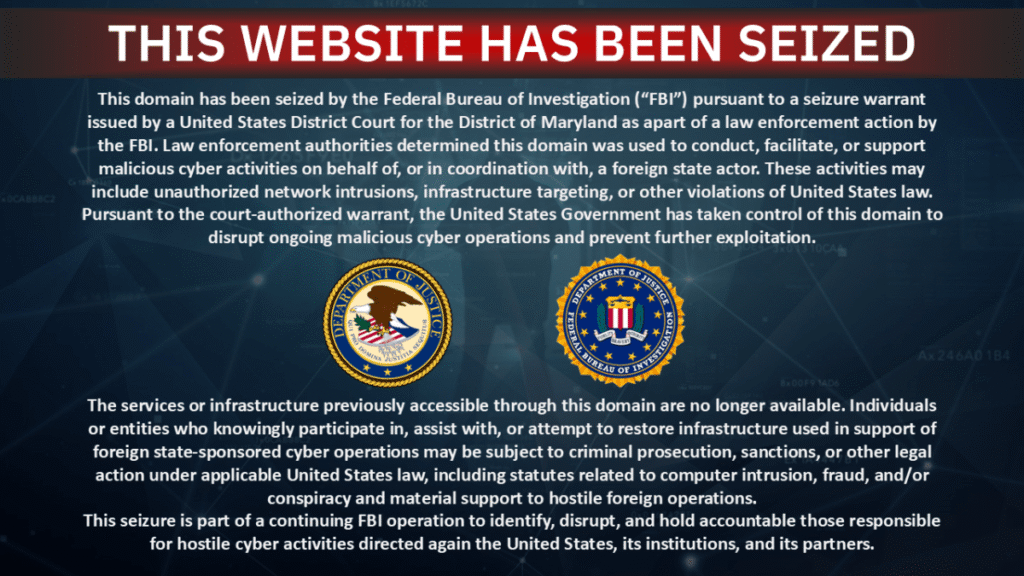
As of Thursday, the content of the website where Handara publicized the hack and another website the group used to keep dozens of people under wraps for alleged ties to Israeli military and defense contractors, including Elbit Systems and NSO Group, had been replaced with banners announcing law enforcement actions.
The seizure announcement did not say why the FBI and Department of Justice shut down the website. But the language appears to indicate that U.S. authorities believe the sites are run by hackers with ties to foreign governments.
“Law enforcement authorities have determined that this domain was used to conduct, facilitate, or support malicious cyber activity on behalf of or in conjunction with a foreign state actor,” the seizure announcement reads. “The U.S. government took control of this domain to disrupt ongoing malicious cyber operations and prevent further exploitation.”
TechCrunch confirmed the seizure of the website by examining its name server records, which point to servers currently controlled by the FBI.
The FBI and Justice Department did not immediately respond to TechCrunch’s requests for comment.

In a series of announcements posted on the group’s official Telegram channel on Thursday, Handara confirmed that the website had been taken offline and called the attack a “desperate attempt to silence our voices.”
“This act of digital attack only highlights the fear and anxiety that our actions instill in the hearts of those we oppress and deceive,” the hackers wrote. “They seek to erase evidence and cover up crimes through censorship and intimidation, but their actions only confirm the impact of our mission. The pursuit of justice will not stop with the removal of a website. The movement for truth will endure and grow stronger.”
Handala’s X account was also recently suspended.
The group did not respond to messages sent to its official chat account.
Handara has been active since at least the October 7, 2023 attack by Hamas and is believed to have ties to the Iranian regime. Last week, the group claimed an attack on Stryker, a U.S. healthcare company with more than 56,000 employees in dozens of countries. The hackers said the hack was in retaliation for a U.S. government missile attack that hit an Iranian school and killed at least 175 people, most of them children.
Last year, Stryker was awarded a $450 million contract to supply medical equipment to the Department of Defense.
Handala reportedly hacked into Stryker’s internal administrator account, giving it nearly unrestricted access to the company’s Windows network. At this point, the hackers allegedly took over Stryker’s Intune dashboard. The dashboard was designed to allow the company to remotely manage employee laptops and mobile devices, and included the ability to delete data.
By accessing these dashboards, hackers were reportedly able to wipe devices owned by both the company and its employees.
Stryker said Tuesday it was still restoring computers and internal networks after the hack.
Nariman Gharib, a UK-based Iranian activist and independent cyber-espionage researcher, told TechCrunch that the takedown is good news.
“Their organizational and administrative structure is currently in disarray, and members of this group, like other cyber units within the regime, could be targeted by missile attacks at any time,” Gharib told TechCrunch.
“But this does not mean that their activities may stop. No, future leaks may be published by this group through media close to the Revolutionary Guards,” he said, referring to the country’s military.
Source link