The year is 2030. A “notorious mystery hacker” known as Puppet Master is wreaking havoc on the Internet, infiltrating the so-called cyber brains of several humans and “every device on the network.” After all, Puppet Master is a creation of Japan’s Ministry of Foreign Affairs.
In other words, Puppet Master is what we would today call a government-sponsored hacker, or Advanced Persistent Threat (APT). However, in this case, the “mysterious” hacker has become the villain, wanted on charges of “stock price manipulation, espionage, political manipulation, terrorism, and cyber brain privacy violation.”
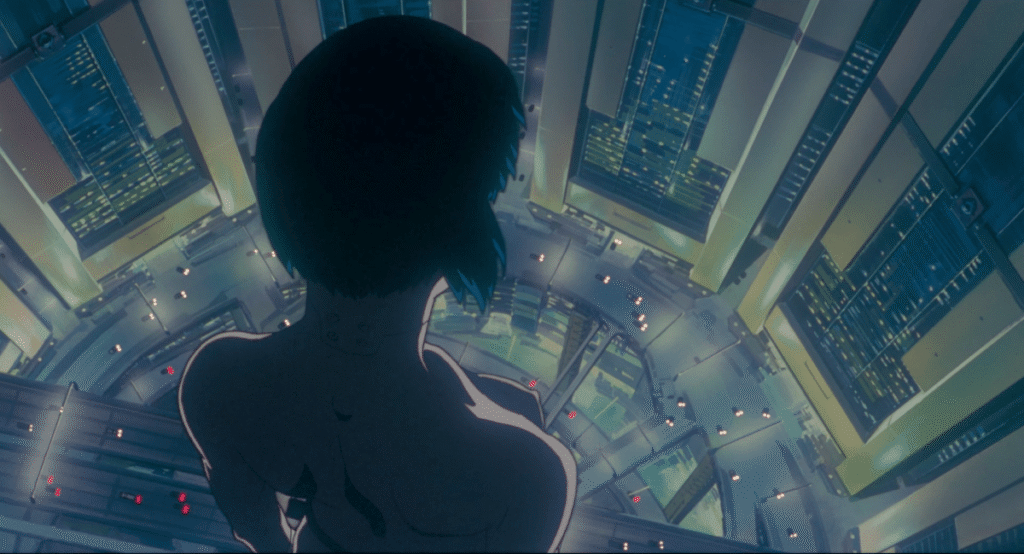
That’s the basic premise of the Japanese cult classic anime “Ghost in the Shell,” which celebrated its 30th anniversary this week and is based on the chapters titled “Bye Bye Clay” and “Ghost Coast” from the first volume of the May 1989 manga of the same name.
It may not be an exaggeration to say that Puppet Master’s story was ahead of its time. The World Wide Web (which evolved from the Internet as we know it today) was invented in 1989. This was the same year that the first volume of the Ghost in the Shell manga (which included the story of the Puppet Master) hit newsstands in Japan. (The World Wide Web was made publicly available in 1991.)

In the comic, when Puppet Master was captured, officials from Public Security Division 6, an agency under the Ministry of Foreign Affairs, explained that they had been tracking the hacker “for a long time” and were “profiling his behavioral trends and code/technical patterns.”
“As a result, we were finally able to create a special anti-puppeteer attack barrier,” a source said in the manga.
Take the risk of inferring too much from a few sentences. In reality, what officials are describing is essentially what cybersecurity companies like antivirus companies do on a daily basis to thwart malware. They create so-called signatures not only based on the malware’s code, but also on its behaviors and characteristics, known as heuristics.
There are other elements of the plot that turn out to be prescient.
At the beginning of Puppet Master’s investigation, Major Motoko Kusanagi, the protagonist and commander of the anti-cyberterrorism unit Section 9, hacks into the Sanitation Bureau’s network in order to track a garbage truck. (These days, government hackers working for intelligence agencies often break into large networks to spy on specific individual targets, rather than siphoning data from the hacked networks themselves.)
Meanwhile, one of the garbage men confesses to his colleague that he hacked into his wife’s computer because he thought she was cheating on him. Shortly thereafter, it is discovered that he was using a computer virus that he had obtained from “a certain programmer.” This is a clear case of technology-enabled domestic violence, and even stalkerware, that TechCrunch has investigated extensively over the past few years.
After all, the abusive trash man didn’t have a wife. His memories were all made up. His ghost, his mind or consciousness, was hacked by the Puppet Master with the purpose of using him to hack government officials. In some ways, this is similar to how some sophisticated hackers hack into a network and then use that network to hack their real target, separating themselves from themselves and their final target to cover their tracks.
Puppet Master as a government hacker, infiltrating networks to track targets or attack other networks, and jealousy-driven hacking are not the only fascinating parts of detective stories related to anime hacking.
John Wilander, a cybersecurity veteran and author of hacker-themed novels, has written an in-depth analysis of the film that focuses on the details and references real-life scenarios. Wilander cited examples of hackers reusing known exploits and malware to make attribution difficult, researching malware and infecting themselves without alerting their creators, and using computers for industrial espionage.
Obviously, the manga and anime take the basic, realistic premise of the Puppet Master as a hacker and take it in a more fantastical direction. This hacker turns out to be an advanced artificial intelligence, capable of controlling humans through his cyberbrain, and, spoiler alert, is self-aware enough to seek political asylum and eventually propose to Kusanagi that he fuse his human “ghost,” or mind.

To understand how prophetic “Ghost in the Shell” was, it’s important to place it in historical context. In 1989 and 1995, the term “cybersecurity” did not yet exist, but the term “cyberspace” was famously coined by science fiction author William Gibson in his classic book “Neuromancer.”
But while computer security, or information security, is already a reality and has been for decades, it was a very niche specialty within computer science.
The first computer virus is believed to be the Creeper worm, which was released in 1971 onto Arpanet, a government-developed network that became the Internet’s predecessor. Several other viruses and worms wreaked havoc after that, but once the Internet and the World Wide Web became a reality, they became ubiquitous.
Perhaps the first government espionage activity documented on the Internet was discovered by Clifford Stoll, a trained astronomer and computer administrator at Lawrence Berkeley National Laboratory in California. In 1986, Stoll noticed a 75-cent accounting error in the network and eventually discovered that hackers had penetrated the lab’s systems. The hackers were eventually identified and found to have been providing information to the Soviet Union’s KGB from the lab and other U.S. government networks.
Stoll immortalized his months of detailed and painstaking research in his book, The Cuckoo’s Egg. This first-person account is like a very detailed and extensive report by a security researcher who analyzed a hacking campaign carried out by government hackers. “The Cuckoo’s Egg” has since become a classic, but it’s safe to say it wasn’t necessarily mainstream at the time it was released.
As far as I know, “Ghost in the Shell” author Masamune Shirow has never said whether real events influenced the hacking plot points in the manga. But it’s clear what he was paying attention to in a hidden world that was alien to most people on the planet back then, who were still years away from being able to connect to the Internet, let alone know that hackers existed.
Source link