Wednesday Interpol announced the dismantling of over 20,000 malicious IP addresses or domains linked to 69 information-stolen malware variants.
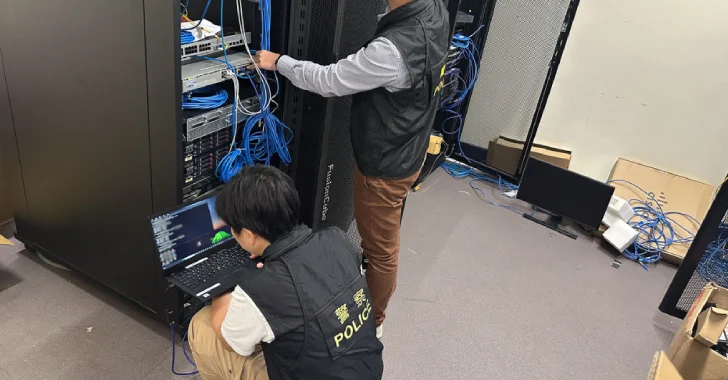
Joint Action, Codename Operation Secure took place between January and April 2025, and involved law enforcement agencies in 26 countries, identifying servers, mapping physical networks, and performing targeted takedowns.
“These coordinated efforts resulted in a takedown of 79% of the suspicious IP addresses identified,” Interpol said in a statement. “Participation countries have reported the seizure of 41 servers and 100 GB of data and the arrest of 32 suspects related to illegal cyber activity.”

Vietnamese authorities arrested 18 suspects, confiscating confiscated devices, SIM cards, business registration documents and money worth $11,500. Further attacks on the house have arrested 12 more people in Sri Lanka and two individuals in Nauru.
Hong Kong police per Interpol have identified 117 command and control servers hosted by 89 internet service providers. These servers are designed to serve as hubs for launching and managing malicious campaigns such as phishing, online scams, and social media scams.

Countries involved in safe operations include Brunei, Cambodia, Fiji, Hong Kong (China), India, Indonesia, Indonesia, Japan, Kazakhstan, Kilibati, Laos, Macau (China), Malaysia, Maldives, Nauru, Nepal, Papua New Guinea, Philippines, Samo, Singapore, Sormon Island, Samo, Samoa, Samoa, Tonga, Vanuatu, and Vietnam.
The development comes just weeks after global operations led to the seizing of 2,300 domains related to Lumma Stealer malware.
Information stealing, often sold on subscription-based Cyber Crime Underground, is considered a stepping stone for threat accessers to gain unauthorized access to their target networks. These malicious programs allow you to siphon up your browser credentials, passwords, cookies, credit card details, and cryptocurrency wallet data from infected machines.

Stolen information is monetized in the form of logs on various forums, allowing other actors to carry out subsequent attacks such as ransomware, data breaches, and business email compromise (BEC).
Group IB, headquartered in Singapore, one of the private companies that Singapore has participated in the operation, said it provided mission-critical intelligence related to user accounts compromised by Stealer Malware, including Lumma, Risepro and Meta Stealer.
“The compromised qualifications and sensitive data obtained by cybercriminals through Infostealer malware often serve as an early vector for financial fraud and ransomware attacks,” said Dmitry Volkov, CEO of Group-IB.
Source link