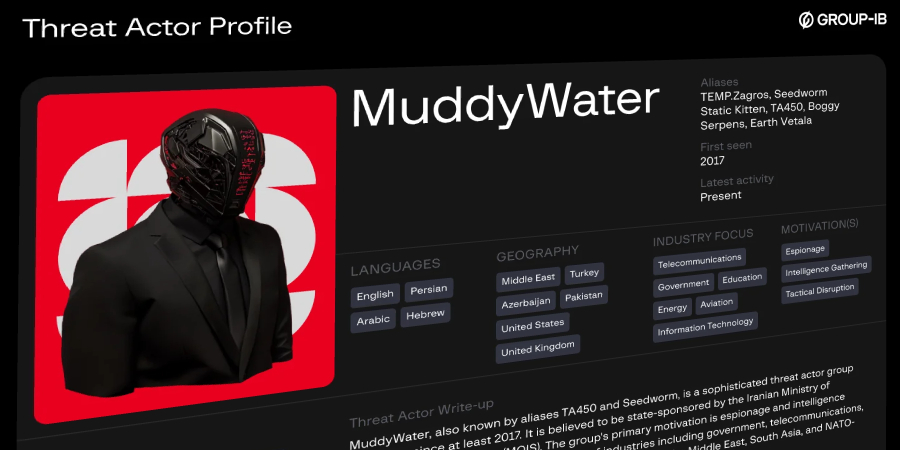
The Iranian hacker group known as MuddyWater (also known as Earth Vetala, Mango Sandstorm, and MUDDYCOAST) targeted multiple organizations and individuals primarily based in the Middle East and North Africa (MENA) region as part of a new campaign codenamed Operation Olalampo.
According to a report published by Group-IB, this activity was first observed on January 26, 2026 and resulted in the deployment of a new malware family that shares overlapping samples previously identified as being used by threat actors. These include downloaders such as GhostFetch and HTTP_VIP, as well as a Rust backdoor called CHAR, and an advanced implant dropped by GhostFetch codenamed GhostBackDoor.
“These attacks follow a similar pattern and are consistent with the kill chain previously observed in the MuddyWater attack. They begin with a phishing email attached with a Microsoft Office document containing malicious macro code that decodes the embedded payload and drops it onto the system for execution, providing the attacker with remote control of the system,” the company said.
One such attack chain uses a malicious Microsoft Excel document that prompts the user to enable macros to activate the infection and ultimately drop the CHAR. Another variant of the same attack has been found to lead to the deployment of the GhostFetch downloader, which downloads GhostBackDoor.
The third version of the attack leverages themes such as airline tickets and reports to distribute an HTTP_VIP downloader that deploys AnyDesk remote desktop software, as opposed to using a lure that mimics a Middle Eastern energy and marine services company.
A brief description of the four tools follows:
GhostFetch is a first-stage downloader that profiles the system, verifies mouse movements, checks screen resolution, checks for the presence of debuggers, virtual machine artifacts, and antivirus software, and fetches and executes secondary payloads directly in memory. GhostBackDoor is a second stage backdoor provided by GhostFetch that supports an interactive shell, file read/write, and GhostFetch rerun. HTTP_VIP, the native downloader that performs system reconnaissance, connects to an external server (“codefusiontech”).[.]org”) to authenticate and deploy AnyDesk from a C2 server. The new variant of this malware also adds the ability to obtain victim information and obtain instructions to start an interactive shell, download/upload files, capture clipboard contents, and update sleep/beacon interval. In the backdoor, change directories and run cmd.exe or PowerShell commands.

The PowerShell commands are designed to run a SOCKS5 reverse proxy or another backdoor named Kalim, upload data stolen from web browsers, and run unknown executables called “sh.exe” and “gshdoc_release_X64_GUI.exe.”
Group-IB’s analysis of CHAR’s source code revealed signs of artificial intelligence (AI)-assisted development due to the inclusion of emojis in the debug string. This is consistent with Google’s revelations last year that threat actors were experimenting with generative AI tools to support the development of custom malware that supports file transfer and remote execution.
Another thing to note is that CHAR is similar in structure and development environment to the Rust-based malware BlackBeard (also known as Archer RAT and RUSTRIC). BlackBeard was reported by CloudSEK and Seqrite Labs to be used by threat actors to target various organizations in the Middle East.
MuddyWater has also been observed exploiting recently revealed vulnerabilities on public servers as a way to gain initial access to target networks.
“The MuddyWater APT group remains an active threat within the META region, and this operation primarily targets organizations in the MENA region,” Group-IB concluded. “The group’s continued adoption of AI technology, development of custom malware and tools, and diversified command and control (C2) infrastructure underscores their dedication and intent to scale their operations.”
Source link