You’ve probably heard of OpenClaw. This open source AI agent quickly became one of the fastest growing repositories in GitHub’s history, gaining over 135,000 stars within a few weeks. However, this led to the first major AI agent security crisis of 2026. Reco helps you identify whether an AI agent is present in your environment.
open claw phenomenon
OpenClaw (previously known as Clawdbot and Moltbot after a trademark dispute) is an open source AI agent created by developer Peter Steinberger. Unlike traditional AI assistants that only answer questions, OpenClaw is autonomous. You can run shell commands, read and write files, browse the web, send email, manage your calendar, and perform actions across your digital life.
Users interact with OpenClaw through messaging platforms such as WhatsApp, Slack, Telegram, Discord, and iMessage. Agents run locally and connect to large language models such as Claude and GPT. Its “persistent memory” feature means it remembers the context of your entire session and learns your preferences and habits over time.
The appeal is obvious. It’s an AI assistant that performs actions on your behalf. People are buying dedicated hardware just to run OpenClaw 24 hours a day. But that ability had serious consequences, and it didn’t take long for them to surface.
Chain of security failures
Within just two weeks of OpenClaw going viral, we saw an increase in the number of security incidents that escalated in both scope and severity. These issues ranged from traditional vulnerabilities to exposed management interfaces and distribution of malicious skills. When considered individually, each is a matter of concern. Taken together, this explains why AI agents with pervasive system access represent a fundamentally new risk category.
January 27-29, 2026 – ClawHavoc
The attacker distributed 335 malicious skills via OpenClaw’s public marketplace, ClawHub. These skills used professional documentation and innocuous names like “solana-wallet-tracker” to appear legitimate, and then instructed users to run external code that installed a keylogger on Windows and Atomic Stealer malware on macOS. Researchers later identified a total of 341 malicious skills out of 2,857. This means that approximately 12% of the entire registry was compromised.
January 30, 2026 – Quiet Patch
OpenClaw has released version 2026.1.29 and patched CVE-2026-25253 before publishing. This vulnerability could allow remote code execution with a single click via a malicious link. This vulnerability exploits the authenticity of URL parameters in the Control UI without validation, allowing an attacker to hijack instances (even instances that are configured to only listen on localhost) through cross-site WebSocket hijacking.
January 31, 2026 – Massive Revelation
Censys identified 21,639 exposed instances that are publicly accessible on the internet, up from about 1,000 a few days ago. The United States accounted for the largest share of published deployments, followed by China, with an estimated 30% of instances running on Alibaba Cloud. We discovered that misconfigured instances were leaking API keys, OAuth tokens, and plaintext credentials.
January 31, 2026 – Maltbook Breach
The same week, Moltbook (a social network built specifically for OpenClaw agents) was discovered to have an insecure database exposing 35,000 email addresses and 1.5 million agent API tokens. The platform has grown to over 770,000 active agents, demonstrating how an unvetted ecosystem can quickly increase risk.
February 3, 2026 – Full disclosure
CVE-2026-25253 was published with a CVSS score of 8.8. On the same day, OpenClaw issued three high-impact security advisories: a one-click RCE vulnerability and two command injection vulnerabilities. Security researchers observed that it takes “milliseconds” for the attack chain to complete after a victim visits a single malicious web page.
Why this matters to your organization
While these technical issues are alarming in and of themselves, the bigger problem is what happens when employees connect personal AI tools to corporate systems, often without the visibility of security teams.
OpenClaw integrates with email, calendar, document, and messaging platforms. Connecting to enterprise SaaS apps like Slack and Google Workspace gives agents access to Slack messages and files, emails, calendar entries, documents stored in the cloud, data from integrated apps, and OAuth tokens that enable lateral movement.
To make matters worse, the agent’s persistent memory means that all data it accesses remains available between sessions. If the agent is then compromised (through a malicious skill, prompt injection, or vulnerability exploit), the attacker inherits all of its access rights.
This is essentially a shadow AI with elevated privileges. Employees are allowing AI agents to access corporate systems without the knowledge or approval of security teams, and each new integration expands the attack surface.
Identify OpenClaw in your environment
Traditional security tools have difficulty detecting AI agent activity. Endpoint Security sees the process running but cannot understand the behavior of the agent. Network tools recognize API calls, but cannot distinguish between legitimate automation and compromise. The identity system recognizes OAuth permissions but does not flag AI agent connections as abnormal.
Reco is one of the few SaaS security platforms that can discover OpenClaw integration throughout your environment.
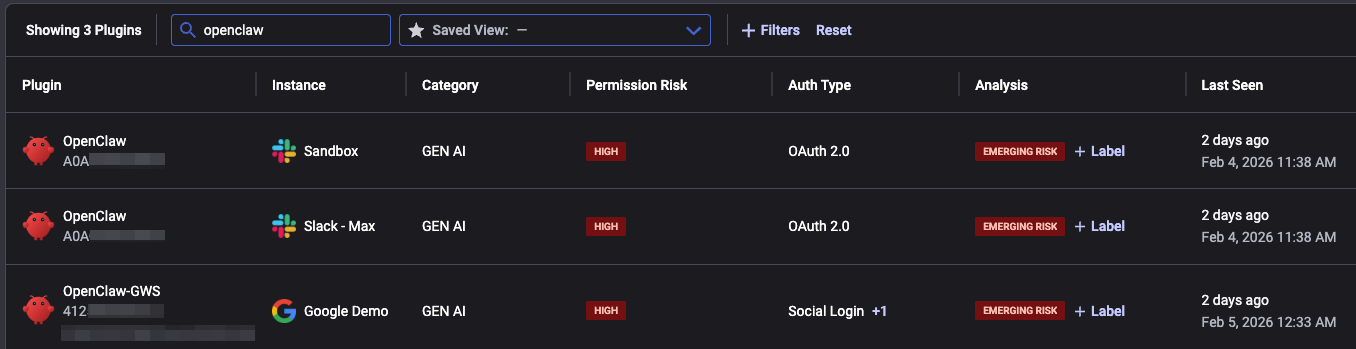
Reco’s plugins page allows you to search all plugins associated with OpenClaw. If an application is associated with a recent instance of an elevated risk pattern, as described below, the associated app will be given an “emerging risk” label.
The SaaS-to-SaaS page provides a graph-based visualization of your organization’s SaaS applications and OpenClaw integration. In this example, you can see OpenClaw being used by both Google Workspace and Slack.
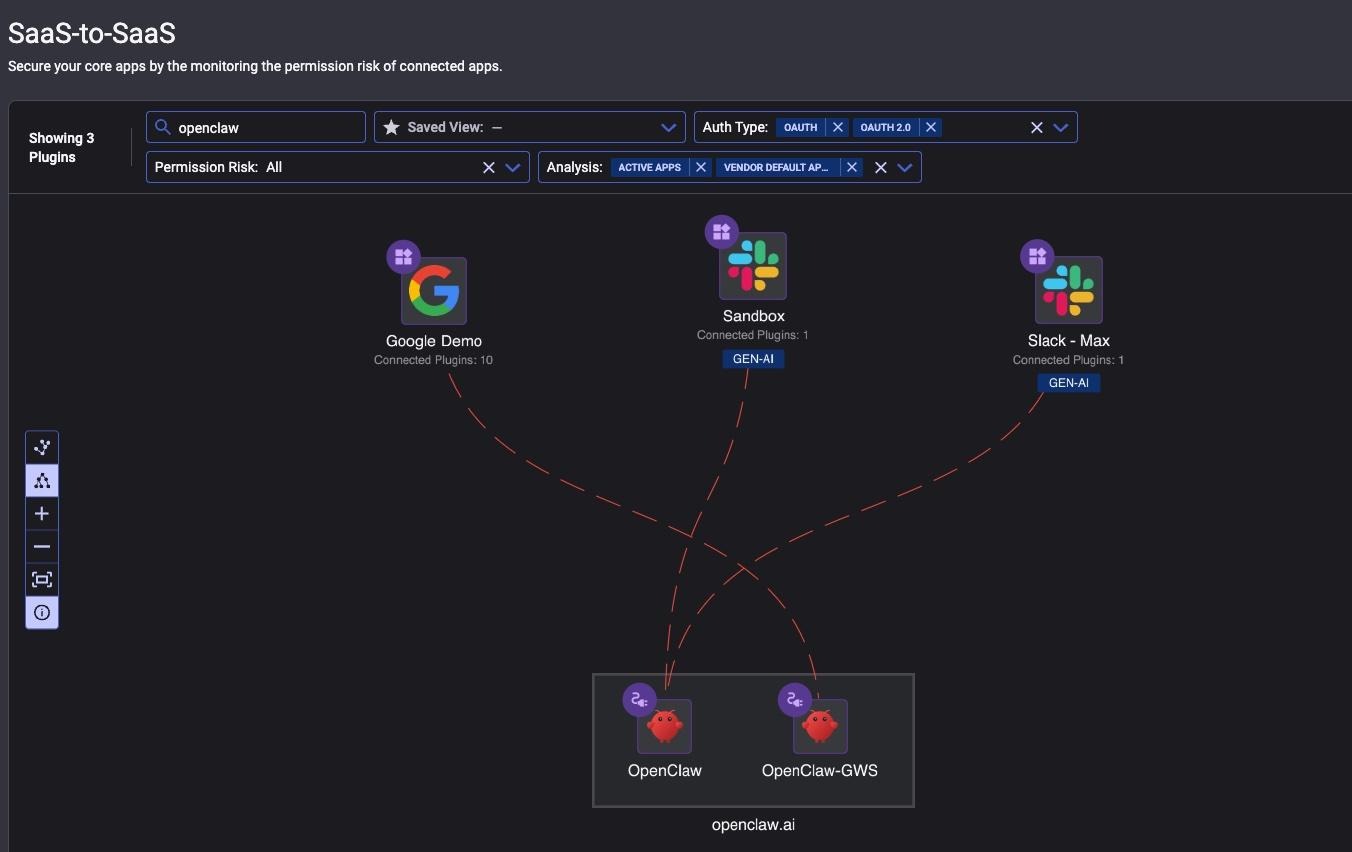
Hover your mouse over the dashed line to see the exact permissions and roles provided to OpenClaw. Reco automatically identifies and flags high-risk permissions such as gmail.modify, gmail.settings.basic, and gmail.settings.sharing, allowing security teams to quickly assess which integrations pose the greatest risk to sensitive data.

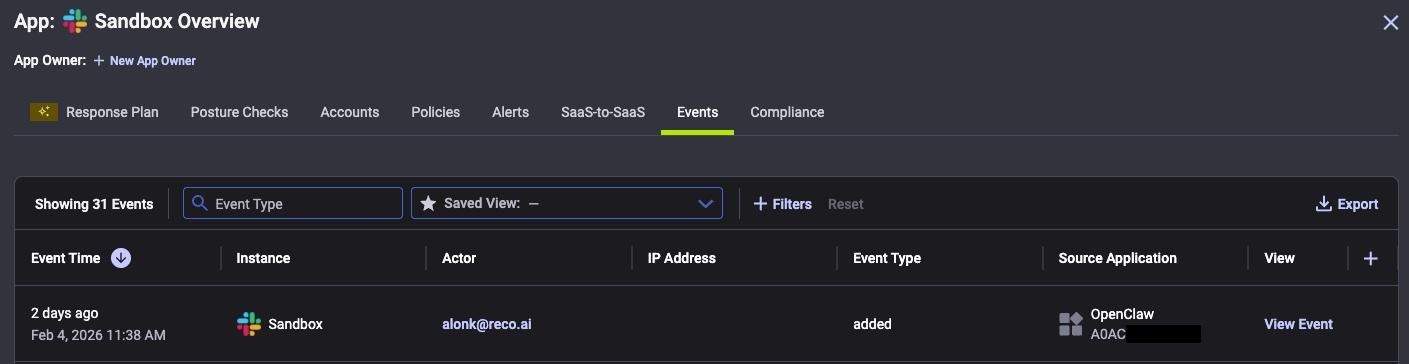
You can use the Events pane if you want to obtain additional details related to the associated application.
This visibility allows security teams to identify AI agent connections, audit which users have granted access, and investigate potential leaks before an incident occurs.
During our investigation, the Reco Security Research team also identified specific user agent strings associated with OpenClaw activity in Slack.
ApiApp/ @slack:socket-mode/2.0.5 @slack:bolt/4.6.0 @slack:web-api/7.13.0 openclaw/22.22.0
This user agent allows you to search for OpenClaw connections directly in your Slack access logs. Although the exact string may vary, this is a useful signal for security teams looking to determine OpenClaw usage across their environments.
big picture
OpenClaw will not be deprecated. Even if it is retired, the demand for autonomous AI agents will mean that another project will replace it.
The productivity benefits are real and employees will continue to adopt these tools regardless of the risks. The security community has called OpenClaw everything from a “security nightmare” to a “dumpster fire,” but its 135,000 GitHub stars make one thing clear: users are willing to accept the tradeoffs.
For security teams, visibility must be a priority. You can’t secure what you can’t see. AI agents are a new category of applications that require new approaches to detection and monitoring, and waiting for the next incident is not a strategy.
To find out if OpenClaw is already connected to your environment, contact us today: https://www.reco.ai/demo-request.
Source link

