Financially motivated threat actors have been linked to a continuous continuous phishing email campaign in July 2024, targeting Polish and German users.
A variety of payloads have been developed by attacks, such as agent Tesla, snake key logger, and tornet, which had been dubbed backdoor unwritten backdoor before being distributed by pure letters. Tornet has been named for the fact that threat actors can communicate with the victim machine via Tor Anony Network.
“The actor is running a Windows scheduled task on a victim machine with low battery endpoints, and has realized sustainability,” said Cisco Talos researcher Chetan Raghuprasad today. It is described in the analysis.

“The actor also cuts the victim machine from the network before dropping the payload, connects to the network, so that it can avoid detection by cloud antimalware solutions.”
The starting point of the attack is a phishing email that contains a fake remittance or ordered book, and the threat actor is pretending to be financial institutions, manufacturing and logistics companies. Attached to these messages is a file equipped with a .tgz, an extension that may avoid detection.

Open the compressed electronic mail attached file and extract the archive content, and when the .NET loader is executed, it is downloaded and executed straight in memory.
The PureCrypter Malware proceeds to the start of the Tonet Backdore, but not before running under the radar, a series of anti -anti -analysis, anti -VM, and malware anti -malware check. 。
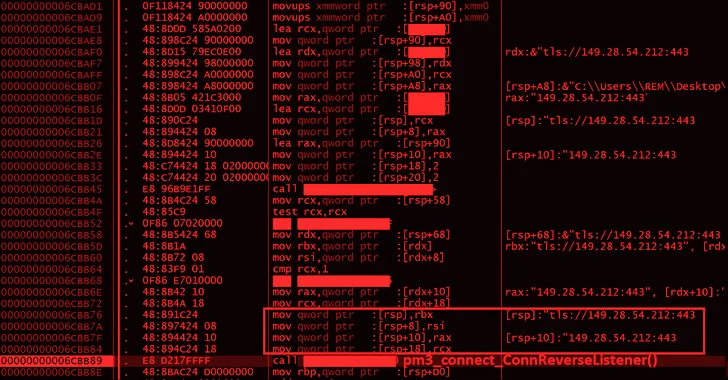
“The Tonet Buckdore establishes a connection to the C2 server and connects the victim machine to the Tor network,” said Raghuprasad. “There is a function to receive any .NET assembly in the memory of the victim machine downloaded from the C2 server, and increase the attack surface for further invasion.”

The disclosure has stated that the threat intelligence company has observed the threat of e -mails utilizing salted text hidden in late 2024, trying to avoid the brand name extraction of the e -mail parser and detection engine. It will happen after a day.
“Hidden Text Salting is a simple and effective technique to bypass e -mail parsers, confuse spam filters, and avoid keyword detection engines,” he said. He says. “The idea is to include some characters in the HTML source of e -mails that cannot be visually recognized.”
In order to counter such an attack, the use of CSS properties such as “visibility” and “display” is detected, and the hidden textbooks are enhanced by adopting a visual similarity detection application (such as PISCO). We recommend that you develop advanced filtering technology that can detect salt and content concealment. Detection function.
Source link