The Russian-linked threat actor known as APT28 (also known as Forest Blizzard) is said to be involved in a new campaign to infiltrate and modify less secure MikroTik and TP-Link routers to take control of malicious infrastructure as part of a cyberespionage campaign since at least May 2025.
This large-scale exploitation campaign, codenamed FrostArmada by Lumen’s Black Lotus Labs, is described by Microsoft as an effort to exploit vulnerable home and small office (SOHO) Internet devices to hijack DNS traffic and enable passive collection of network data.
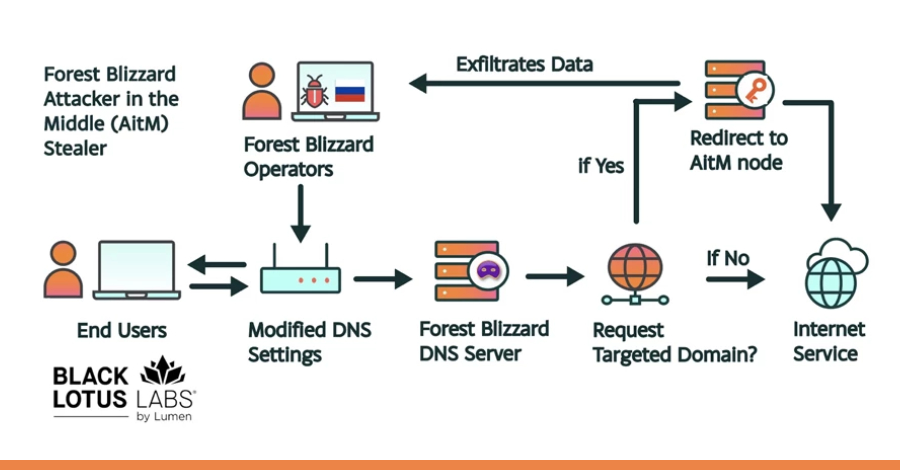
“Their method changed the DNS settings of compromised routers to hijack local network traffic and capture and exfiltrate authentication credentials,” Black Lotus Labs said in a report shared with The Hacker News.
“Once the targeted domain was claimed by a user, the attacker redirected the traffic to an attacker-in-the-middle (AitM) node, where these credentials were collected and exfiltrated. This approach enabled a nearly invisible attack that required no end-user interaction.”
As part of a joint operation with the U.S. Department of Justice, Federal Bureau of Investigation, and other international partners, infrastructure associated with the campaign was disrupted and taken offline.
This activity is assessed to have started on a limited scale in May 2025, followed by widespread router abuse and DNS redirection beginning in early August. At its peak in December 2025, over 18,000 unique IP addresses from over 120 countries were found communicating with the APT28 infrastructure.
These efforts primarily target government agencies such as the Ministry of Foreign Affairs, law enforcement agencies, and third-party email and cloud service providers in North Africa, Central America, Southeast Asia, and European countries.
In analyzing the campaign, the Microsoft Threat Intelligence team attributed this activity to APT28 and its subgroup tracked as Storm-2754. The tech giant announced that it has identified more than 200 organizations and more than 5,000 consumer devices affected by the threat actor’s malicious DNS infrastructure.
“For nation-state attackers like Forest Blizzard, DNS hijacking enables persistent, passive visibility and large-scale reconnaissance,” Redmond said. “By compromising edge devices upstream of large-scale targets, attackers can leverage assets that are less closely monitored or managed to gain entry into enterprise environments.”

DNS hijacking activity also facilitates AitM attacks, facilitating the theft of passwords, OAuth tokens, and other credentials for web and email-related services, putting organizations at risk for widespread compromise.
Microsoft added that this development marks the first time that a hostile group has been observed using DNS hijacking at scale to support AiTM for Transport Layer Security (TLS) connections after exploiting edge devices.
Broadly speaking, the attack chain involves APT28 gaining remote administrative access to a SOHO device and changing the default network configuration to use a DNS resolver under its control. The malicious reconfiguration causes the device to send a DNS request to an attacker-controlled server.
This allows DNS lookups for email applications or login pages to be resolved by a malicious DNS server. Threat actors then attempt to perform AitM attacks against these connections in order to steal user account credentials by tricking victims into connecting to malicious infrastructure.
Some of these domains are associated with Microsoft Outlook on the web. Microsoft said it also identified AitM activity targeting non-Microsoft hosted servers in at least three government agencies in Africa.
The UK’s National Cyber Security Center (NCSC) said: “DNS hijacking operations are thought to be opportunistic in nature, with attackers gaining visibility into a large pool of potential target users and then attempting to filter users at each stage of the exploitation chain to triage victims likely to have intelligence value.”
APT28 is said to have exploited TP-Link WR841N routers for DNS poisoning operations by leveraging the authentication bypass vulnerability CVE-2023-50224 (CVSS score: 6.5). This vulnerability can be used to extract stored credentials via a specially crafted HTTP GET request.
A second cluster of servers was found to receive DNS requests through a compromised router and then forward them to a server owned by a remote attacker. This cluster was also assessed to be conducting interactive operations targeting a small number of MikroTik routers in Ukraine.
“Forest Blizzard’s DNS hijacking and AitM activity enabled attackers to conduct DNS harvesting against sensitive organizations around the world, consistent with the attackers’ long-standing mission to collect espionage against priority intelligence targets,” Microsoft said.
“Although we have only observed that Forest Blizzard uses DNS hijacking campaigns for intelligence gathering, attackers may use AiTM’s location for additional outcomes such as malware deployment or denial of service.”
Source link