The cybersecurity landscape is accelerating at an unprecedented rate. What is emerging is not just an increase in the number of vulnerabilities and tools, but a dramatic increase in velocity. The speed of attacks, speed of exploitation, and speed of change in modern environments.
This is the defining challenge of the new era of digital warfare: the weaponization of artificial intelligence. From nation-states to sophisticated criminal enterprises, threat actors no longer just attack. They are automating the entire kill chain.
In this AI arms race, traditional defense strategies are no longer sufficient. Regular point-in-time assessments, manual triage, and human-speed responses were already under pressure in a fast-moving environment. AI is becoming increasingly inadequate against AI-powered adversaries.
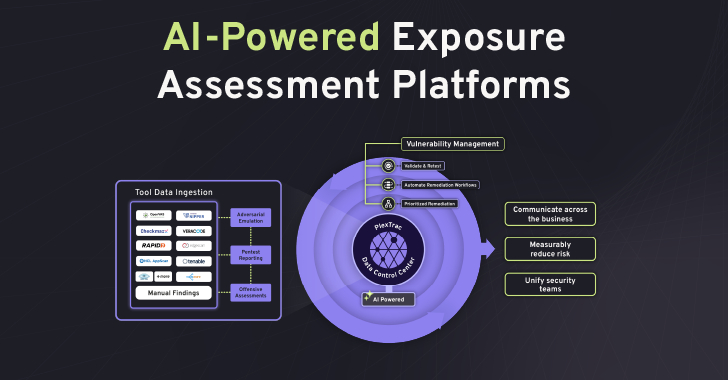
Solutions like PlexTrac are built to help organizations overcome fragmented findings, disconnected tools, and slow manual workflows by consolidating exposure management, remediation, and validation into a single operational system. As the gap between discovery and exploitation continues to shrink, security teams need a way to continually assess risks, prioritize what’s important, and take action quickly enough to keep up.
In order to use AI to counter adversaries, defenders must also use AI. Specifically, two key capabilities need to be integrated: autonomous exposure assessment and continuous threat assessment powered by Agentic AI.
Modern Adversaries – AI in the Threat Actor’s Armory
To understand defense, you need to understand offense.
AI has become a power multiplier for threat actors. Attackers are using generative AI to create targeted phishing campaigns at scale. They use machine learning to analyze defenses, automatically identify vulnerabilities, and chain complex attack vectors faster than human operators. Perhaps most alarming is the rise of polymorphic malware, which can rewrite its own code in real time to evade signature-based detection.
Gone are the days of manually researching and discovering vulnerabilities, determining whether one or more vulnerabilities can be chained together, and determining whether they can be used to reach a target. Now, AI-powered automation can compress that cycle into hours or even days.
This means threat actors are now operating faster, stealthier, and more efficiently than ever before.
Stay ahead with integrated exposure management
1. Sustainable autonomous exposure assessment
In this high-velocity environment, understanding the attack surface is the foundation of defense. But traditional vulnerability management is broken. It’s too slow, too noisy, and produces flat, disconnected data.
This is where AI-powered exposure assessment platforms like PlexTrac become important.
PlexTrac serves as a sensory system for modern defense strategies. Don’t just scan for CVEs. Ingest data from across your ecosystem, including cloud misconfigurations, identity risks, application defects, and penetration test results to create a unified, dynamic risk view.
PlexTrac enables organizations to:
cut noise
Rather than overwhelming your team with thousands of “critical” alerts, apply contextual scoring to prioritize vulnerabilities that actually pose a significant risk.
Visualize attack paths
Let’s look beyond isolated findings and see how attackers can chain together seemingly minor weaknesses into domain-wide compromises.
Moving from reactive to proactive
Using automated assessments and predictive insights to identify where risks are likely to occur next, teams can strengthen their defenses before attacks occur.
2. Continuous threat assessment with Agentic AI
Exposure assessments provide visibility, but visibility alone is only a prerequisite for action. To stay ahead of the AI arms race, organizations need autonomous and continuous validation. This is where Agentic AI comes into play.
Agentic AI represents a meaningful transition from traditional AI co-pilots. Agent systems can plan, reason, and execute multi-step tasks with greater autonomy, rather than waiting for prompts.
This transforms continuous threat assessment from a concept to a practical capability.
autonomous penetration testing
Agentic AI acts as a synthetic red teamer, allowing you to continuously test your defenses. You can simulate the latest AI-driven attack techniques in real-time without sleep or fatigue.
This includes the following features:
Plan and adapt attack vectors
Rather than running a static checklist, these systems can analyze network topology, prioritize targets, and construct multi-step attack paths. If it encounters an obstacle, it can adjust its tactics in a manner much like a skilled human operator.
emulate the behavior of an adversary
These systems can emulate known TTPs or simulate new AI-powered attack techniques using underlying models trained on large-scale threat intelligence.
Validate the effectiveness of your defense stack
You can continually test whether your SIEM, EDR, and XDR tools are actually detecting the right behavior and alerting the right users, providing evidence of defensive effectiveness rather than expected coverage.
Adapt in real time
As network configurations change or new threat intelligence emerges, the agent system can update its evaluation logic and testing procedures to respond to the real-world threat environment.
By automating many of the red team’s repetitive tasks, organizations can free up human operators to focus on truly novel, sophisticated, and subtle attack vectors.
3. Close the loop – AI-driven remediation and validation
It’s not enough to discover a vulnerability if it takes weeks to fix it. Attackers exploit this delay.
This is why PlexTrac’s role in closing the loop is so important. Exposure control cannot be terminated after detection. It should extend to remediation and validation.
Once an exploitable path is identified, AI-enabled workflows within the exposure management platform allow you to take action on it faster.
Instant context and ticket creation
As soon as the critical path is validated, a detailed remediation ticket is generated in a system like Jira or ServiceNow, including steps to reproduce, severity context, and any required actions.
Automatic policy updates
If your firewall is misconfigured, you can draft the required configuration changes and prepare them for human approval before deployment.
Integrated patch management
For critical vulnerabilities, workflows can prioritize patches and support testing in staging, accelerating deployment and reducing mean time to remediation.
automatic verification
Agents can verify whether controls put in place to remediate issues are actually effective, allowing teams to reduce risk while getting better value from their existing security stack.
PlexTrac gives organizations the ability to fight AI with AI by integrating Agentic AI-powered red teaming, remediation, and verification into its exposure management platform. This is how security teams move from continuous vulnerability to provable continuous posture assurance.
A new path towards cybersecurity resilience
Cybersecurity resiliency relies on proactive insights, continuous validation, and the ability to migrate faster than manual workflows. The goal is to move from a chaotic, reactive posture to one that is intentional, resilient, and measurable.
PlexTrac is focused on helping security teams make that transition by combining integrated exposure management with AI-driven capabilities that automate tedious tasks, consolidate fragmented efforts, and accelerate action.
The AI arms race is here.
The question is no longer whether your organization will be targeted by threat actors using AI. The question is whether they can develop the resilience, foresight, and limited autonomy necessary to endure them.
Note: This article was expertly written and contributed by Rohit Unnikrishnan, Chief Product and Technology Officer at PlexTrac. Rohit is an experienced cyber security executive with a background in product management, market analysis, strategy, sales, and engineering. Over the past 20 years, he has held a variety of roles including engineer, operator, sales, product manager, and entrepreneur. His diverse experience brings a unique ability to manage cross-functional teams and execute multidisciplinary initiatives.
Source link