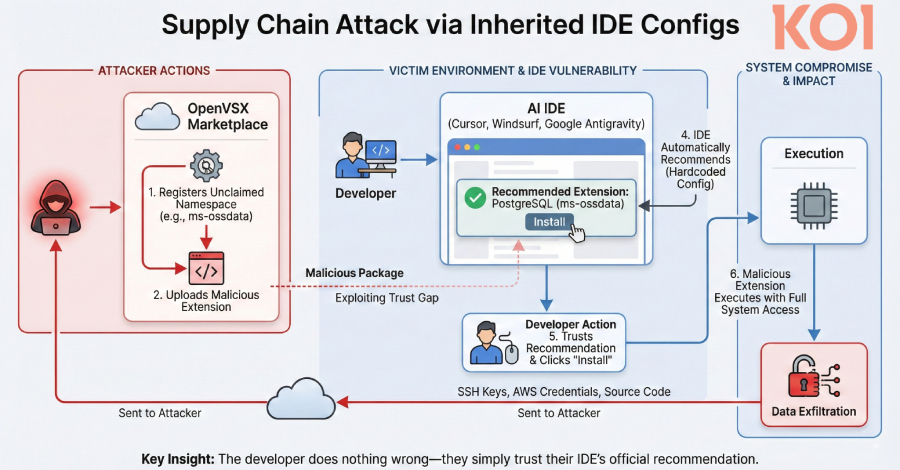
Popular artificial intelligence (AI)-powered Microsoft Visual Studio Code (VS Code) forks such as Cursor, Windsurf, Google Antigravity, and Trae have been found to promote extensions that are not present in the Open VSX registry, potentially opening the door to supply chain risk if bad actors publish malicious packages with these names.
The problem, Coy said, is that these integrated development environments (IDEs) inherit a list of officially recommended extensions from Microsoft’s extension marketplace. These extensions do not exist in Open VSX.
VS Code extension recommendations come in two different formats. One is file-based, which appears as a toast notification when the user opens a file in a particular format, and the other is software-based, which is suggested when a particular program is already installed on the host.
“The problem is that these recommended extensions were not present in Open VSX,” said Oren Yomtov, a security researcher at Koi. “Namespaces were not required. Anyone could register a namespace and upload anything they wanted.”

This means that an attacker could take advantage of the absence of these VS Code extensions and the fact that the AI-powered IDE is a VS Code fork to upload malicious extensions such as ms-ossdata.vscode-postgresql to the Open VSX registry.
As a result, whenever a developer with PostgreSQL installed opens one of the aforementioned IDEs and sees a “Recommended: PostgreSQL extension” message, a simple installation action results in a rogue extension being deployed to the system instead.
This simple act of trust can have serious consequences, potentially leading to the theft of sensitive data such as credentials, sensitive information, and source code. Coy said the company’s placeholder PostgreSQL extension has attracted more than 500 installations, indicating that developers are downloading the extension simply because their IDE suggested it as a recommendation.
Some of the extension names claimed by Koi are listed below with placeholders.
ms-ossdata.vscode-postgresql ms-azure-devops.azure-pipelines msazurermtools.azurerm-vscode-tools usqlextpublisher.usql-vscode-extcake-build.cake-vscode pkosta2005.heroku-command

In response to responsible disclosure, Cursor, Windsurf, and Google have published fixes that address this issue. The Eclipse Foundation, which oversees Open VSX, has since removed unofficial contributors and applied broader registry-level protections.
As threat actors increasingly look to exploit security gaps in extension marketplaces and open source repositories, it’s important for developers to exercise caution before downloading a package or approving it for installation by ensuring it comes from a trusted publisher.
Source link