Non-human employees are becoming the future of cybersecurity, and businesses need to prepare accordingly. As organizations expand artificial intelligence (AI) and cloud automation, non-human identities (NHI) such as bots, AI agents, service accounts, and automation scripts are rapidly increasing. In fact, in ConductorOne’s 2025 Future of Identity Security report, 51% of respondents said the security of their NHI is now as important as the security of their human accounts. However, despite their presence in modern organizations, NHIs often operate outside of traditional identity and access management (IAM) systems.
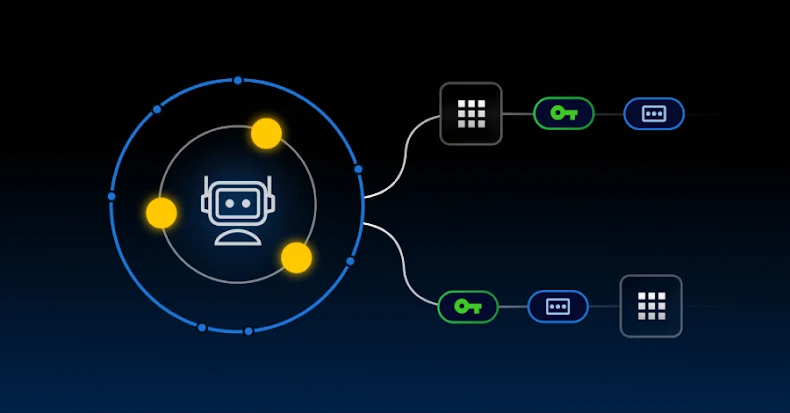
This increased reliance on non-human users creates a new attack surface that organizations must urgently prepare for. Without full visibility and proper monitoring, NHI can have overly permissive, persistent access and static credentials, making it a valuable target for cybercriminals. To protect NHIs with the same precision as human identities, organizations must develop modern security strategies that incorporate zero trust security, least privilege access, automatic credential rotation, and confidentiality management. By modernizing their strategies, organizations can work to reduce security risks and prevent privileged account compromises, whether the users are human or not.
Why non-human identities increase cybersecurity risks
Unlike human users, NHIs and their activities typically go unnoticed, despite having powerful access to sensitive systems. NHIs are often granted broad and persistent access across infrastructure, cloud environments, and CI/CD pipelines. Once access to NHI is provided, it is rarely reviewed or revoked, making it a prime target for cybercriminals. Key security risks associated with NHI include hard-coded credentials in scripts, secrets embedded in source code, and lack of visibility into how NHI is being used. There is often little logging or monitoring of NHI, making it easy for compromised machine credentials to be exploited and allowing cybercriminals to remain undetected for weeks or even months. In cloud environments, non-human users greatly outnumber human users, expanding the attack surface and introducing more security vulnerabilities. If NHI is overlooked in security audits or excluded from traditional IAM policies, security teams risk the convenience of automation becoming a huge blind spot.
How to protect non-human access with zero trust principles
To mitigate NHI-related security risks, organizations must apply zero-trust security to all identities by treating bots, AI agents, and service accounts the same as humans. The main ways Zero Trust security protects non-human access are:
Enforce zero trust for machine users: All NHIs must be authenticated and authorized, and only allowed the minimum necessary access. All activity must be able to be recorded, monitored, and audited to ensure compliance with regulatory requirements. Enforce least-privilege access: Assign role-based access control (RBAC) and set time-based credential expiration policies to ensure NHIs only have access to what they need, when they need it. Leverage just-in-time (JIT) access and temporary secrets: Eliminate persistent access by replacing static credentials with short-lived API tokens. Additionally, automate the rotation of credentials after a task is completed or according to a set schedule.
Implementing some of these practices can significantly reduce exposure to NHI and enable auditing and management of NHI at scale. For example, auto-expiring API tokens after deployment minimizes the risk of those secrets being misused. The same goes for service accounts that do not maintain permanent access, but only request access when needed for a specific task. By operationalizing these practices, organizations can effectively manage NHI with the same level of control as human users in a Zero Trust architecture.
Manage secrets and privileged access at scale
Secrets such as API keys, tokens, and SSH credentials are important for automation and NHI, but if not managed properly, they create significant security vulnerabilities. To maintain control over sensitive information and privileged access, organizations need to know who accesses what, when, and which resources. Without such detailed insight, unmanaged secrets can spread throughout your environment if hard-coded into scripts, stored securely in plain text, or shared without tracking or expiration.
Fortunately, organizations can use secrets management and privileged access management (PAM) solutions to centrally manage both secrets and privileged access. Solutions like KeeperPAM® provide a zero-trust, zero-knowledge architecture that protects credentials, monitors privileged sessions, and automatically rotates credentials across your cloud infrastructure. As an integrated solution, KeeperPAM brings together enterprise password management, secrets management, and endpoint management to protect both human and non-human users equally.
Identity security must extend beyond human identity
As enterprise infrastructures become more modern and automated, national health insurance has become a permanent part of the attack surface. To protect against more sophisticated cyber-attacks, organizations must treat non-human employees as first-class identities, securing and managing them just like human employees. All service accounts, scripts, and AI agents must be secured and continuously monitored to ensure they are granted appropriate access to the required data and systems. To stay ahead of NHI-related cyber threats, organizations must embed Zero Trust principles across all access layers, both human and machine.
Note: This article was professionally written and contributed by Ashley D’Andrea, Content Writer at Keeper Security.
Source link