A newly discovered Vietnam-related operation was observed using Google AppSheet as a “phishing relay” to distribute phishing emails aimed at compromising Facebook accounts.
The operation was codenamed AccountDumpling by Guardio, and the plan was to sell stolen accounts back through illegal storefronts operated by threat actors. In total, it is estimated that approximately 30,000 Facebook accounts were hacked as part of the campaign.
“What we discovered was not a single phishing kit,” security researcher Shaked Chen said in a report shared with Hacker News. “It was a living operation with a real-time operator panel, advanced evasion, continuous evolution, and criminal and commercial loops that silently preyed on the same accounts to help steal back.”
This finding is just the latest example of how Vietnamese threat actors continue to employ a variety of tactics to gain unauthorized access to victims’ Facebook accounts and then sell them in the underground ecosystem for financial gain.
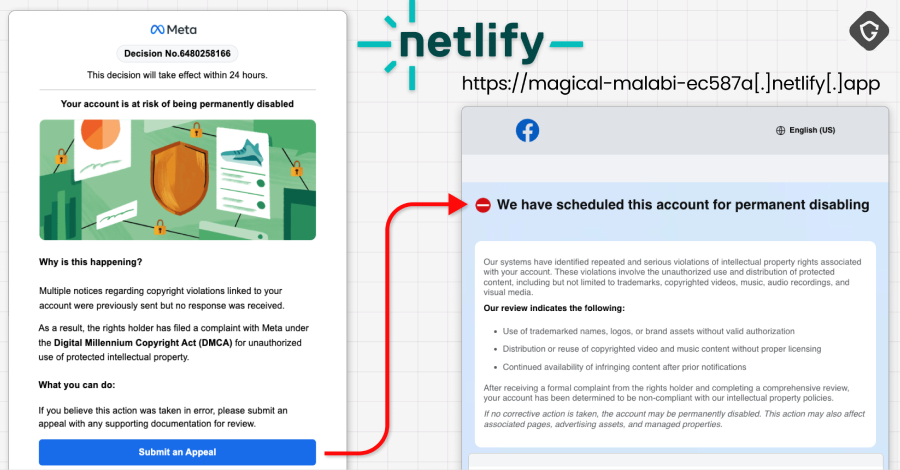
The starting point for the latest attack is a phishing email targeting Facebook Business account holders claiming to be from Meta Support and urging them to file a dispute or risk having their account permanently deleted. The email is sent from a Google AppSheet address (“noreply@appsheet.com”), allowing it to bypass spam filters.
This false sense of urgency is used to lure users to fake web pages designed to collect credentials. It is worth noting that a similar campaign was reported by KnowBe4 in May 2025.

Over the past few weeks, these campaigns have employed various types of lures designed to induce “meta-related panic.” These range from account deactivations and copyright claims to verified reviews, executive hiring, and Facebook login alerts. The four main clusters identified by Guardio are listed below.
Netlify-hosted Facebook Help Center pages collect dates of birth, phone numbers, government-issued ID photos, and enable account takeover attacks. The data is ultimately transferred to a Telegram channel controlled by the attacker. A blue badge rating directs victims to a Vercel-hosted “Security Check” or “Meta | Privacy Center” page. These pages are gated with fake CAPTCHA checks to collect contact details, business information, credentials (after forced retries), and two-factor authentication (2FA) codes before directing users to phishing landing pages and exfiltrating them to Telegram channels. A PDF hosted on Google Drive disguises as instructions to complete account verification and instructs users to collect passwords, 2FA codes, government ID photos, and browser screenshots through html2canvas. PDF documents are generated using a free Canva account. Fake job offers impersonating companies such as WhatsApp, Meta, Adobe, Pinterest, Apple, and Coca-Cola to build trust with recipients and ask them to join a call or continue a discussion on an attacker-controlled site.
Cumulatively, Telegram channels related to the first three clusters were found to contain records of approximately 30,000 victims, most of whom are located in the United States, Italy, Canada, Philippines, India, Spain, Australia, United Kingdom, Brazil, and Mexico, and whose accounts are locked out.
Conclusive evidence as to who is behind this operation comes from a PDF generated as part of the third cluster using a free Canva account, whose metadata lists the Vietnamese name “PHẠM TÀI TÂN” as the file’s author. Further open source intelligence resulted in the discovery of a website (“phamtaitan”).[.]vn”) provides digital marketing services.
In a post shared on X in February 2023, the website handle said it “specializes in providing digital marketing services, marketing resources, and consulting on effective digital marketing strategies.”

“Taken together, these form a coherent picture of a large-scale mega-operation based in Vietnam,” Chen said. “This campaign is larger than any single AppSheet exploit. It’s a window into the black market for stolen Facebook assets, where access, business identity, advertising reputation, and even account recovery are all tradable goods. It’s another entry into a pattern we continue to surface: trusted platforms repurposed as a distribution, hosting, and monetization layer.”
Source link