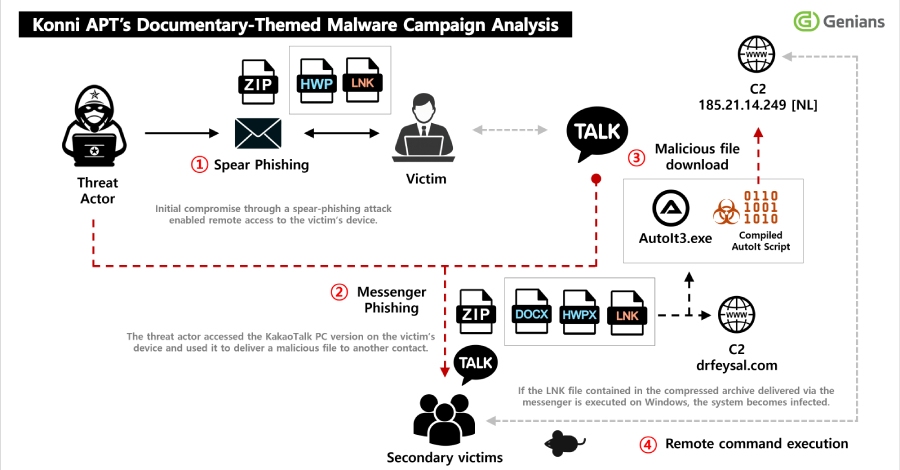
North Korean attackers have been observed sending phishing attacks to compromise targets, gain access to victims’ KakaoTalk desktop applications, and distribute malicious payloads to specific contacts.
South Korean threat intelligence firm Genians attributes this activity to a hacker group called Konni.
“Initial access was achieved through a spear-phishing email disguised as a notification appointing the recipient as a human rights lecturer in North Korea,” Jennians Security Center (GSC) said in an analysis.
“After a successful spear-phishing attack, the victim executed a malicious LNK file, which resulted in infection with remote access malware. The malware remained hidden on the victim’s endpoint for an extended period of time, persisting, and exfiltrating internal documents and sensitive information.”
The attacker allegedly remained on the compromised host for an extended period of time, used unauthorized access to siphon internal documents, and utilized the KakaoTalk application to selectively propagate malware to specific contacts.
This attack is notable in that it exploits the trust associated with compromised victims to deceive and entrap further targets. This isn’t the first time Konni has embraced messaging apps as a distribution vector. In November 2025, the hacker group was discovered to be abusing signed-in KakaoTalk chat app sessions to send malicious payloads to victim contacts in the form of ZIP archives, while simultaneously initiating remote wipes of Android devices using stolen Google credentials.
The starting point for the latest attack campaign is a spear phishing email used as a ruse to trick recipients into opening a ZIP file attachment containing a Windows shortcut (LNK). Once executed, the LNK file downloads the next stage payload from an external server, uses a scheduled task to establish persistence, and finally executes the malware. At the same time, it displays a PDF decoy document to the user as a distraction mechanism.

The downloaded malware written with AutoIt is a remote access Trojan (RAT) named EndRAT (also known as EndClient RAT) that allows operators to remotely take over compromised hosts through features such as file management, remote shell access, data transfer, and persistence.
Further analysis of the infected hosts revealed the presence of various malicious artifacts, including AutoIt scripts for RftRAT and RemcosRAT. This indicates that the attacker deemed the victim valuable enough to remove multiple RAT families to improve resiliency.
A key aspect of this attack is that the threat actor exploits the victim’s KakaoTalk application installed on the infected system, distributing malicious files in the form of ZIP files to other individuals in their contact list and deploying the same malware. This essentially turns existing victims into vectors for further attacks.
“This campaign is assessed to be a multi-stage campaign that goes beyond simple spear phishing, combining long-term persistence, information theft, and account-based redistribution,” Jennians said. “The attacker selected specific contacts from the victim’s friends list and sent additional malicious files. At the time, the attacker used a file name disguised as material promoting North Korea-related content to induce the recipient to open the file.”
Source link