Cybersecurity researchers are sounding the alarm about a new supply chain attack campaign targeting SAP-related npm packages that contain credential-stealing malware.
According to reports from Aikido Security, SafeDep, Socket, StepSecurity, and Google-owned Wiz, the campaign, dubbed Mini Shai-Hulud, affected the following packages related to SAP’s JavaScript and cloud application development ecosystem:
mbt@1.2.48 @cap-js/db-service@2.10.1 @cap-js/postgres@2.2.2 @cap-js/sqlite@2.2.2
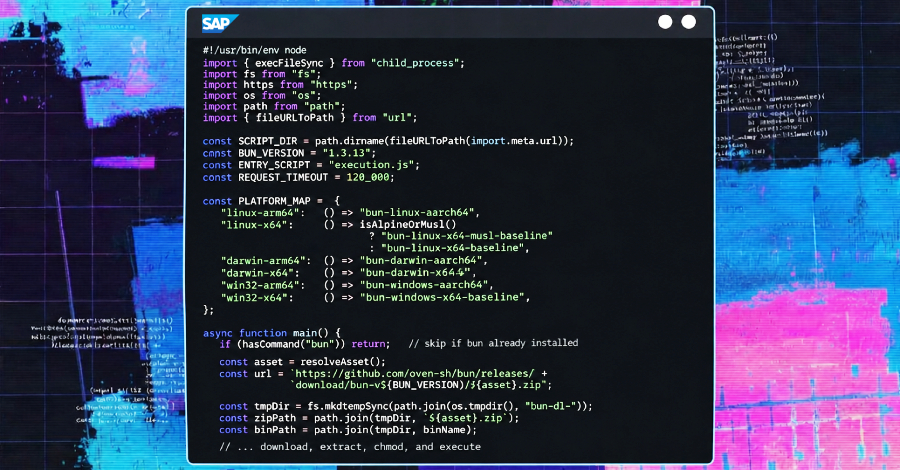
“The affected versions introduced new behavior during installation that was not previously part of the expected functionality of these packages,” Socket said. “Compromised releases have added preinstallation scripts that act as runtime bootstrappers, downloading and unpacking platform-specific Bun ZIPs from GitHub releases, and immediately running the extracted Bun binaries.”
“This implementation follows HTTP redirects without validating the destination and uses PowerShell with -ExecutionPolicy Bypass on Windows, increasing risk for affected developers and CI/CD environments.”
Wiz noted that the malicious package matches several features present in previous TeamPCP operations, indicating that the same threat actor is likely behind the latest campaign.
The suspicious version was published between 09:55 UTC and 12:14 UTC on April 29, 2026. The tainted package introduces a new package.json preinstallation hook that executes a file named ‘setup.mjs’. This hook acts as a loader for the Bun JavaScript runtime and executes the credential stealer and propagation framework (‘execution.js’).
According to Aikido, the malware is designed to collect local developer credentials, GitHub and npm tokens, GitHub Actions secrets, and cloud secrets from AWS, Azure, GCP, and Kubernetes. The stolen data is encrypted and leaked to a public GitHub repository created under the victim’s own account with the caption “A Mini Shai-Hulud has Appeared.” At the time of writing, there are over 1,100 repositories with descriptions.
Additionally, the 11.6 MB payload comes with the ability to self-propagate through developer and release workflows, specifically using GitHub and npm tokens to inject a malicious GitHub Actions workflow into the victim’s repository, stealing the repository’s secrets, and publishing poisoned versions of npm packages to the registry.
However, this incident is very different from the previous Shai Huld wave.
All leaked data is encrypted with AES-256-GCM and encapsulated using RSA-4096 with a public key embedded in the payload, effectively making it only decryptable by an attacker. This exists in the Russian locale system. This payload commits to all accessible GitHub repositories by injecting a “.claude/settings.json” file that exploits Claude Code’s SessionStart hook and a “.vscode/tasks.json” file with “runOn”: “folderOpen” settings. This will cause the malware to run when you try to open an infected repository in Microsoft Visual Studio Code (VS Code) or Claude Code.
“This is one of the first supply chain attacks to target AI coding agent configurations as a persistence and propagation vector,” StepSecurity said.
Further analysis of the root cause revealed that the attacker compromised RoshniNaveenaS’s account for three “@cap-js” packages, then pushed the modified workflow to a non-main branch and used the extracted npm OIDC token to publish a malicious package of unknown origin. As for mbt, it is suspected that the compromise of the “cloudmtabot” static npm token via an as-yet-unidentified channel is involved.
“The cds-dbs team transitioned to npm OIDC trusted publishing in November 2025,” SafeDep said. “This configuration allows GitHub Actions to request short-lived npm tokens without storing long-lived secrets in the repository. The attacker manually reproduced this exchange in a CI step and outputted the resulting token.”
“Critical configuration gap: npm’s OIDC trusted publisher configuration for @cap-js/sqlite was trusting all workflows in cap-js/cds-dbs, not just the main canonical release-please.yml. If the workflow has id-token: write permission and an environment: npm reference, branch pushes can exchange OIDC tokens on behalf of the package.”
In response to this incident, the package maintainer released a new secure version to replace the compromised release.
Source link