Every security team has a version of the same story. The quarter ends with hundreds of vulnerabilities resolved. The dashboard is full of green. Then someone in the leadership council asks, “So are we actually safer now?”
Crickets.
The room falls silent because honest answers require context. Patch counts and CVSS scores are not designed to provide context. Exposure management was created to provide this context – to bridge the gap between remediation efforts and actual risk mitigation. The market responded with a flood of platforms claiming to offer just that. But the question security leaders are asking is which exposure management platforms actually offer that?
In this article, we categorize the four main approaches to exposure management, explain what each can and cannot offer, and provide five metrics to help you differentiate between platforms built to reduce risk to your own business or environment from those built to report real risk.
Four approaches, four architectures
Most exposure management platforms fall into one of four categories, and each category is formed by how the vendor builds (or combines) the platform and how it processes the data.
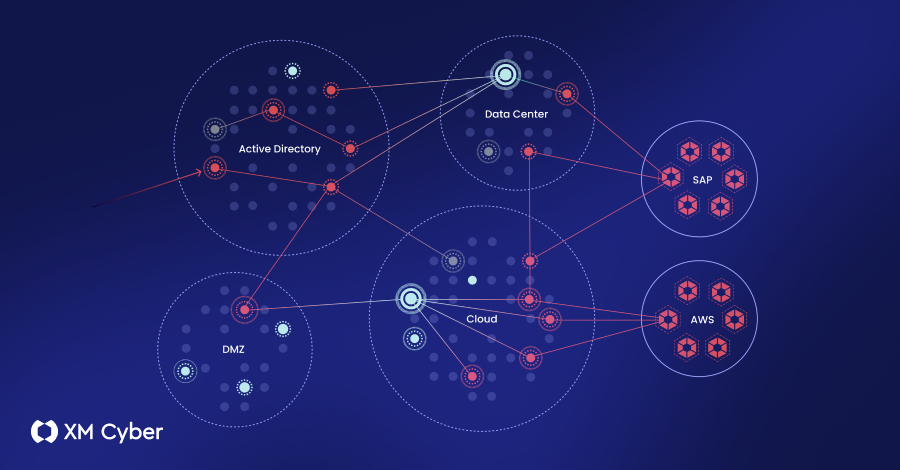
The consolidated portfolio platform is the product of an acquisition. Vendors buy point solutions such as cloud security, vulnerability scanning, and identity analytics and bundle them with their own brand. In these platforms, each product maintains its own data model and discovers its own subset of exposures. Vendors may then consolidate exposures in a shared console, which may look like consolidation. But in reality, each module still processes its own data and produces its own results, but there is little correlation or interconnection between modules. Data aggregation platforms ingest findings from existing scanners and third-party tools. Next, normalize the data and display it in a unified interface. These platforms only work with what they receive. That is, if captured findings are disconnected, there is no way to correlate how one exposure enables the next. A single-domain, specialized platform delves deep into one area: cloud misconfigurations, network vulnerabilities, identity compromise, and external attack surfaces. They deliver powerful results, but only in certain areas of expertise. When exposures in one domain cascade to exposures in another domain, the platform faces the challenge of not having a way to model that relationship. The unified platform is built from the ground up to detect and correlate multiple risk types such as credentials, misconfigurations, CVEs, identity issues, and cloud configurations within the same engine. The platform builds a digital twin of your environment and maps how attackers move laterally from one exposure to the next across on-premises, cloud, and hybrid boundaries.
5 questions that reveal what the platform can actually do for you
The architecture behind each of the four approaches has a real impact on what teams can see, verify, and act on. How do you tell the difference when evaluating? Start by asking these five questions:
1. How many types of exposure are there that can be detected, and how deeply can each be analyzed?
CVEs account for approximately 25% of exposures exploited by attackers. The rest is made up of misconfigurations, cached credentials, excessive permissions, and identity vulnerabilities. The combined portfolio is limited to what each product acquired was built to find. Aggregators can only normalize what the feed provides. A single domain platform covers only one slice of the pie. The integration platform should natively cover both existing and (especially) new exposure types, such as AI workloads and machine identity.
And reporting alone is not enough. What the platform actually knows about each exposure is equally important. Platforms that ingest results from third-party tools are limited to the metadata (exploitability status, remediation guidance, and investigations) that those tools collect. Exposure discovery platforms natively control every layer of information for each discovery, from exploitability to remediation. There is a blind spot when a platform cannot recognize certain exposure types. If you see them but lack depth, you’re working with noise.

2. Can you map attack paths across your environment?
Some stitched products also have attack paths marked. These paths are derived from the network topology and are based solely on connectivity. The platform does not model how attackers actually move laterally from one exposure to the next. The aggregator does not generate any paths at all, only a normalized list of disconnected results.
The real test is whether the platform can trace paths across environment boundaries. Once an attacker obtains cloud credentials on-premises, they can bypass all cloud-native defenses. This is because the path begins outside the visibility of the cloud platform. An externally facing vulnerability may seem like a low priority on its own, but when it maps to an internal entity with a path to a critical asset, it is an emergency. Most platforms do not allow you to draw these connections. They scan each environment independently, leaving gaps between them unknown.
3. Verify exploitability?
Most platforms check one or two conditions per exposure, but this is limited by the metadata they store for each result and the information they collect from each entity in the environment. But true validation means testing multiple conditions. Is the vulnerable library loaded by a running process? Is the port open and reachable? Platforms should provide binary answers based on the actual environment, not general assumptions, such as exploitable or not, reachable or not, path to critical assets or not.
4. Are security controls considered?
Vulnerabilities in CVSS 9.8 blocked by firewalls cannot be used for lateral movement because they are blocked. 5.5 Identity compromise through a direct path to a domain controller is an emergency. Platforms that ignore firewalls, MFA, EDR, and segmentation can cause teams to chase findings that pose no real risk and miss findings that actually threaten critical assets. If your security controls are not included in your attack path analysis, your prioritization is misguided and you are still at risk.
5. How are priorities set?
Prioritizing requires answering one question: “Will this exposure put my critical assets at risk?” Score-based rankings ignore your unique circumstances. Asset tag-based ranking ignores assets within the exposure blast range. The assumed path rankings are not tested for exploitability. All three can overwhelm IT teams because they can’t connect findings to what the business actually needs to protect.
Effective prioritization starts with critical assets and works backwards. Platforms must prove that the exposure is exploitable, that attackers can get there, and that the path leads to something the company can’t afford to lose. When a platform maps all of this into a single graph, the pain points appear, where a single fix eliminates multiple attack vectors. In large enterprise environments, the priority list is narrowed down to approximately 2% of all exposures.
What this means for your team
Your platform architecture choices will determine how secure your environment will be and how your team will spend their time getting there. Connected and aggregated platforms leave teams scrambling to reconcile findings across tools, fighting with IT over remediations that may not mitigate risks, and tracking down hazards that lead to dead ends. Single-domain platforms provide depth in one area but leave blind spots in the rest of the attack surface.
An integrated approach eliminates that overhead. Correlate exposures to validated attack paths, consider the elements of controls in place, and identify remediation that eliminates the greatest risk with the least amount of action. As remediation resolves chokepoints, the continuous exposure management platform updates graphs in real-time. This way, you’ll know that risks that once seemed urgent are now leading nowhere, and your priority queue will always reflect current risks.
If an exposure management platform can validate exploitability, model security controls, and map every viable path to critical assets, then the question at the beginning of this article (Is it actually safe?) can be answered with an honest “yes!”
Note: This article was thoughtfully written and contributed by Maya Malevich, Director of Product Marketing at XM Cyber.
Source link