Cybersecurity researchers are sounding the alarm over alleged “malicious activity” in a newly released version of node-ipc.
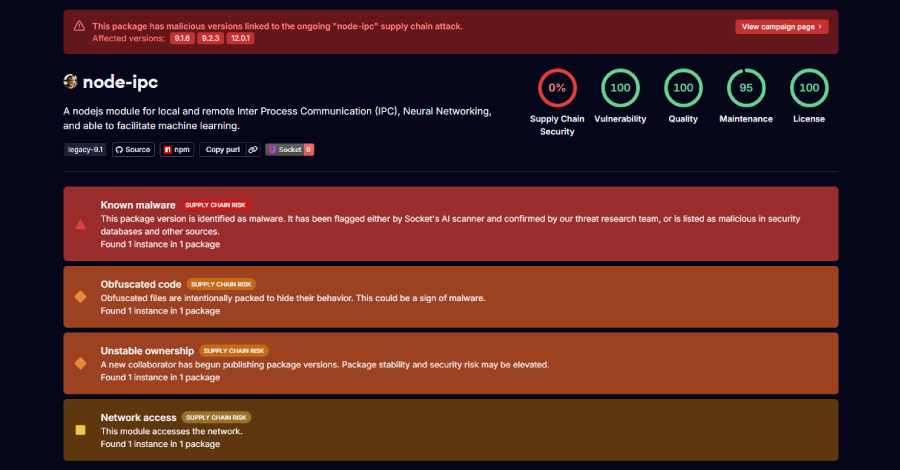
According to Socket and StepSecurity, three different versions of npm packages have been confirmed as malicious.
node-ipc@9.1.6 node-ipc@9.2.3 node-ipc@12.0.1
“Initial analysis indicates that node-ipc@9.1.6, node-ipc@9.2.3, and node-ipc@12.0.1 contain obfuscated stealer/backdoor behavior,” Socket said.
“The malware appears to attempt to fingerprint the host environment, enumerate and read local files, compress and chunk the collected data, wrap the payload in a cryptographic envelope, and exfiltrate it through network endpoints selected by DNS/address logic.”
According to StepSecurity, the highly obfuscated payload is triggered when the package is needed at runtime and attempts to exfiltrate a wide range of developer and cloud sensitive information to external command and control servers.
This isn’t the first time npm packages have included malicious functionality. In March 2022, the package’s maintainers intentionally introduced destructive functionality into versions 10.1.1 and 10.1.2 by overwriting files on systems located in Russia or Belarus as part of a protest against Russia’s military invasion of Ukraine.
Two subsequent versions (11.0.0 and 11.1.0) included the “peacenotwar” dependency, which was also published by the same maintainer as a “nonviolent protest against Russian aggression.”
“This incident appears to be related to the suspicious re-publishing or reintroduction of malicious code into a known package version, rather than an attempt at typosquatting,” Socket said.
(This is a developing story. Check back for more details.)
Source link