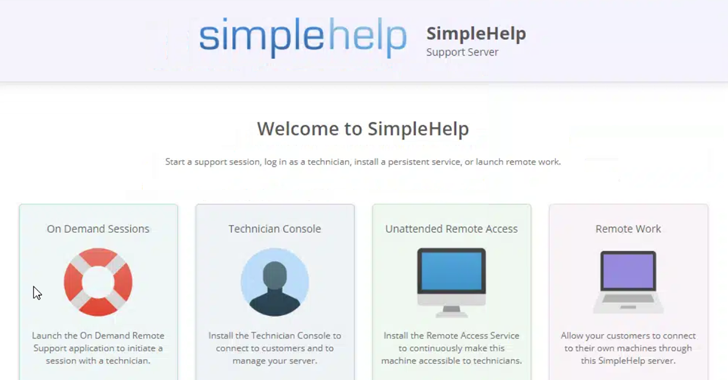
Threat actors have recently been observed to harness the recent disclosed security flaws in SimpleHelp’s Remote Monitoring and Management (RMM) software to portray what appears to be a ransomware attack.
Intrusions have now exploited patched vulnerabilities to gain initial access and maintain persistent remote access to unspecified target networks, and cybersecurity company field effects have been shared with hacker news This is stated in the report.
“Attacks include network and system discovery, creating administrator accounts, and establishing persistent mechanisms that could lead to ransomware deployment. It involved rapid and intentional execution,” said security researchers Ryan Slaney and Daniel Albrecht.

The vulnerabilities in question, CVE-2024-57726, CVE-2024-57727, and CVE-2024-57728, were disclosed last month by Horizon3.AI. The successful exploitation of security holes allows for information disclosure, escalation of privileges, and execution of remote code.
It has since been addressed in SimpleHelp versions 5.3.9, 5.4.10, and 5.5.8, released on January 8th and 13th, 2025.
Just a few weeks later, Arctic Wolf said it had observed a campaign that involved gaining unauthorized access to devices running SimpleHelp Remote Desktop Software as an initial access vector.
At the time, it was unclear whether these vulnerabilities were used, but the latest findings from the Field confirm that they are actively weaponized as part of the ransomware attack chain.
In an incident analyzed by a Canadian cybersecurity company, the initial access was acquired to the target endpoint via a vulnerable SimpleHelp RMM instance (194.76.227).[.]171″) Located in Estonia.
Once a remote connection is established, the threat actor performs a series of post-exposure actions, including reconnaissance and discovery operations, and creates an administrator account named “SQLADMIN” to facilitate the deployment of the open source sliver framework It has been observed.
The persistence provided by Sliver is then abused to move the network sideways, establishing a connection between the domain controller (DC) and the vulnerable SimpleHelp RMM client, and eventually installing the CloudFlare tunnel. stealth routes traffic to the server under attacker’s control over the web. Infrastructure Company infrastructure.
Field effects have shown that attacks were detected at this stage, preventing attempted tunnel execution from occurring, and allowing the system to be isolated from the network to further compromise.
If the event is not flagged, the CloudFlare tunnel could have served as a conduit for obtaining additional payloads containing ransomware. The company said the tactics overlap with previously reported Akira ransomware attack tactics in May 2023, but it also said that other threat actors may have adopted commercial operations.

“This campaign provides just one example of how threat actors can actively leverage simple RMM vulnerabilities to gain unauthorized, persistent access to networks of interest,” the study said the person. “Organisations exposed to these vulnerabilities should consider adopting cybersecurity solutions to update their RMM clients as quickly as possible and protect against threats.”
The development reveals an increasing use of Screen Connect RMM software on bulletproof hosts as a way for threat accessers to access and control victim endpoints as a way for them to access and control victim endpoints. did.
“Potential attackers are using social engineering to induce victims and install legitimate software copies configured to operate under threat actor control,” the company says. Ta. “Once installed, an attacker can use the modified installer to quickly access the victim’s files.”
Source link