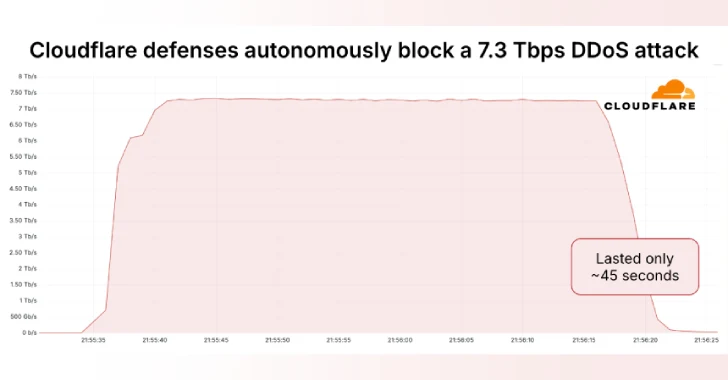
CloudFlare said Thursday it autonomously blocked the largest ever recorded distributed denial-of-service (DDOS) attack, reaching a peak of 7.3 terabits per second (TBPS).
The attack, detected in mid-May 2025, targeted an unknown hosting provider.
“Hosting providers and critical internet infrastructure are increasingly becoming targets for DDOS attacks,” said Omer Yoachimik of CloudFlare. “The 7.3 TBPS attack provided 37.4 terabytes in 45 seconds.”
Earlier this January, the web infrastructure and security company said it had mitigated a 5.6 TBPS DDOS attack targeting unnamed Internet Service Providers (ISPs) in East Asia. The attack came from the Mirai-Variant Botnet in October 2024.
Then, in April 2025, CloudFlare revealed it defended against a massive 6.5 Tbps flood that is likely to emanate from the Eleven11bot, a botnet made up of around 30,000 webcams and video recorders. The ultra-sound measurement attack lasted approximately 49 seconds.

By comparison, the 7.3 TBPS DDOS attack, in a carpet bombing, bombing an average of 21,925 destination ports on a single IP address owned and used hosting providers, hitting the summit of 34,517 destination ports per second.
Multivector attacks stem from similar distributions of source ports and have been identified as a combination of UDP flooding, QOTD reflex attacks, echo reflex attacks, NTP reflex attacks, Mirai UDP flooding attacks, port map flooding, and RIPV1 amplification attacks. The UDP flood accounted for 99.996% of attack traffic.
CloudFlare also pointed out that the attack came from over 122,145 source IP addresses spanning 5,433 autonomous systems (AS) across 161 countries. The biggest sources of attack traffic included Brazil, Vietnam, Taiwan, China, Indonesia, Ukraine, Ecuador, Thailand, the US and Saudi Arabia.
“The average number of unique source IP addresses per second was 26,855, with a peak of 45,097,” Yoachimek said.
“Telefonica Brazil (AS27699) accounted for the largest portion of DDOS attack traffic, taking charge of 10.5% of the total. ViettelGroup (AS7552) continued closely at 9.8%, while China Unicom (AS4837) and Chunghwa Telecom (AS3462) (AS3413) contributed 3.9% and 2.9% of traffic.
Disclosures arise when the QIANXIN XLAB team stated that the DDOS botnet was tracked as the rapper bot was tracked behind an attack targeting artificial intelligence (AI) company DeepSeek in February 2025, and that it was behind an attack that attempted to avoid “protection fees” to pay victims “protection fees” to prevent future DDOS attacks from targeting them.
China, the US, Israel, Mexico, the UK, Greece, Iran, Australia, Malaysia and Thailand are the major countries with devices infected with rapperbots. The botnet is known to be active since 2022.

The Rapperbot campaign is known to target routers with default weak passwords or firmware vulnerabilities, network-mounted storage devices, and video recorders with firmware vulnerabilities that get initial access, and drop malware that can establish contact with remote servers via DNS TXT records to obtain DDOS attack commands.
Malware uses custom encryption algorithms to encrypt the TXT records and command and control (C2) domain names used.
“Since March, its offensive behavior has been significantly more active, with an average of over 100 attack targets and over 50,000 bots observed per day,” a Chinese security vendor said.
“The targets of rapperbots’ attacks lie in a range of industries, including public management, social security, social organization, internet platforms, manufacturing, and financial services.”
Source link