A coordinated international operation involving U.S. and Chinese authorities has resulted in the arrest of at least 276 suspects and the closure of nine fraud centers used in a cryptocurrency investment fraud scheme targeting Americans, resulting in millions of dollars in losses.
The crackdown was led by Dubai Police, part of the United Arab Emirates (UAE) Ministry of Interior, in collaboration with the US Federal Bureau of Investigation (FBI) and China’s Ministry of Public Security. Those arrested included people from Burma and Indonesia, who were arrested by authorities in Dubai and Thailand.
Thet Min Nee, 27, Willian Awan, 23, Andreas Chandra, 29, Lisa Mariam, 29, and two fugitive co-conspirators were indicted in the United States on federal fraud and money laundering charges.
“Scammers targeting Americans from abroad cannot operate with impunity, no matter where they live in the world,” said Assistant Attorney General A. Theisen Duba of the Justice Department’s Criminal Division. “Fraud center organizers and scammers who defraud Americans and others will be tried in American courts and courtrooms around the world. In modern society, fraud knows no borders, and so do law enforcement efforts to combat and eradicate it.”
According to the indictment, the defendants allegedly operated, worked for, and hired employees from three different companies: Ko Thet Company, Sanduo Group, and Giant Company, which allegedly operated multiple fraud centers. Thet Min Nyi is believed to be a manager and recruiter at Ko Thet Company.
The scam involves building trust over time and then tricking users into parting with their money through fake cryptocurrency investments, often by entering into a friendly or romantic relationship, a long-running scheme known as pig slaughter or romance baiting. This illegal activity is closely intertwined with human trafficking, in which foreigners are recruited with false offers of well-paid jobs and then forced to perform fraudulent acts under slave-like conditions.
“The scammers then facilitated investments in cryptocurrencies, helping victims open false accounts and transfer cryptocurrencies to investment platforms without their knowledge,” the Justice Department said. “The alleged scammers promoted their successes and profits in cryptocurrency investments and encouraged victims to invest further. They also encouraged victims to borrow money from friends and family or take out loans so they could further ‘invest.’”
However, as soon as the funds were transferred to the platform, the assets were laundered into other crypto accounts, some of which belonged to the scammers.
The Department of Justice said following the launch of an initiative called “Operation Level Up,” which began in January 2024 as a way to proactively identify and warn victims of cryptocurrency investment fraud schemes, the FBI has notified approximately 9,000 victims and saved victims an estimated $562 million as of April 2026.
Two Chinese people charged with cryptocurrency fraud
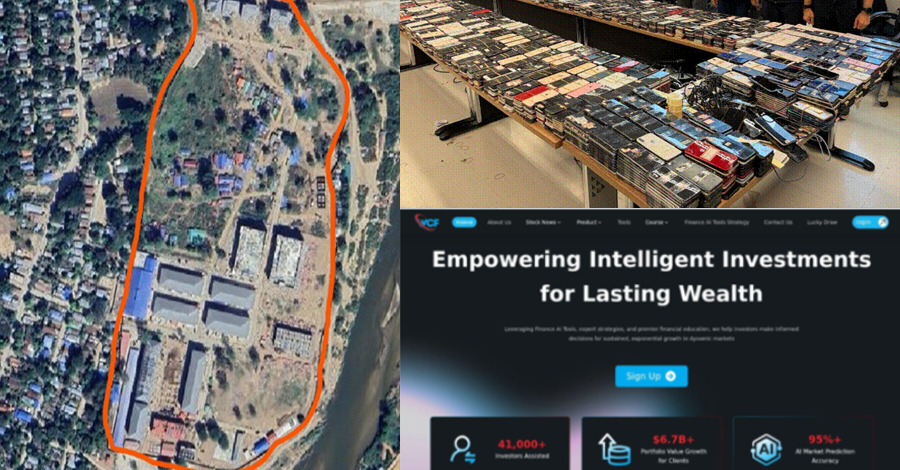
News of the indictment comes days after the Department of Justice indicted two Chinese nationals, Chiang Wenjie (also known as Jiang Nan) and Huang Xingshan (also known as Ah Ze and Fan Hsing San), for their involvement in a large-scale cryptocurrency investment fraud operation and for allegedly operating a Shunda fraud facility in Minlepan, Myanmar. The defendants are also suspected of planning to open a second fraud center in Cambodia after Burmese authorities seized the first one in November 2025.
Mr. Huang worked as a senior manager at Shunda and is credited with personally participating in the corporal punishment of multiple trafficked workers, while Mr. Jiang served as a team leader overseeing workers who specifically targeted American victims in these schemes. They were arrested by Thai authorities in early 2026 while en route from Cambodia to Burma.

“The compound defrauded victims, including Americans, using fraudulent websites and mobile applications masquerading as legitimate investment platforms,” the Justice Department said. “The workers at the site were trafficked people who were held against their will and forced to defraud their victims under threat of violence and torture.”
Additionally, the crackdown resulted in the seizure of a Telegram channel (@pogojobhiring2023) with more than 6,500 followers that was used to recruit human trafficking victims to fraudulent facilities in Cambodia to commit law enforcement impersonation fraud, and a cluster of 503 fake investment websites used to defraud victims in the United States. The action, led by the U.S. government’s Fraud Center Strike Force, also resulted in the suppression of more than $701 million in cryptocurrencies allegedly linked to money laundering through crypto fraud.
Treasury sanctions on Cambodian senators
Coinciding with these efforts, the U.S. Treasury Department sanctioned a Cambodian senator behind a network of cyber fraud conglomerates, and the State Department announced a reward of up to $10 million for information leading to the seizure or recovery of proceeds related to Burma’s Tay Trang fraud center.
The sanctions target Cambodian senator Kok An, Cambodian businessman Rithy Lakmei, their associates, and their respective business operations, including holding companies such as K99 Group, which operates a fraud center. Kokuan is believed to have fled Thailand, and authorities issued arrest warrants for him and his children in July last year.
The Office of Foreign Assets Control (OFAC) said, “Koch Quang and its network of affiliated fraud centers operate out of fraudulently modified casinos and office parks, laundering victims’ funds, targeting U.S. citizens, and providing a base for human rights abuses with impunity.”
Kok An is the second Cambodian senator to be sanctioned by the US Treasury, following Lee Yong Huat, who was implicated in September 2024 for allegedly trafficking people into forced labor at an online fraud center.
In response to a surge in industrial-scale fraud, Cambodia’s parliament has passed the first law aimed at targeting fraud centers operating in the country. The law is aimed at preventing fraud centers from resurfacing after being busted, and those convicted of fraud would face five to 10 years in prison and fines of up to $250,000.
Cambodian fraud complex related to Android MaaS
Additionally, an Android banking Trojan was discovered. The Trojan is likely operating from multiple locations, including the K99 Triumph City complex owned by K99 Group in Cambodia, and could facilitate real-time surveillance, credential theft, data exfiltration, and even financial fraud. This banking Trojan has reportedly been in use since at least 2023.
According to a joint report by Infoblox and Vietnamese nonprofit organization Chong Lua Dao, this sophisticated malware-as-a-service (MaaS) platform overlaps in infrastructure and behavior with activity by threat actors previously tracked as Vigorish Viper and Vault Viper.
“This activity remains active, registering approximately 35 new domains per month, both Registered Domain Generation Algorithm (RDGA) domains and lookalike domains, distributing malware by impersonating legitimate organizations and government services,” the researchers said.
“These domains are designed to impersonate banks, pension funds, social security institutions, public utilities, various revenue agencies, immigration authorities, telecommunications agencies, and law enforcement agencies. Recently, the scope of the scam has expanded both geographically and situationally, to include decoys targeting airlines, e-commerce platforms, and even African and Latin American countries.”
A total of 400 targeted lure domains were allegedly registered in 2025 and used to trick and infect victims as part of a coordinated operation. The attack chain is as follows:
Malicious URLs are distributed to users through SMS messages or emails that appear to come from government officials. Victims visit a fake Google Play Store app listing page or government services website. Once the APK is installed and launched, privileges are elevated to facilitate persistence. The malware connects to external servers and allows operators to remotely monitor victims’ devices and collect data. Attackers insert fake overlay screens on online banking apps to obtain credentials and use that access to transfer funds to accounts under their control.
“Activities related to this infrastructure continue to adapt and expand, increasingly diversifying into Africa and Latin America, while continuing large-scale campaigns targeting countries such as Thailand, Indonesia, the Philippines, and Vietnam,” Infoblox and Chong Lua Dao noted.
“With large, multilingual workforces, growing technological capabilities, and access to vast profits, they are not only adapting and commoditizing malware, infrastructure, and social engineering techniques into versatile and scalable attack models. What is emerging is an agile, experimental, and commercially driven ecosystem where tools are continually reused, refined, and redeployed to maximize reach and profit.”
$12 million seized in Operation Atlantic
The development comes against the backdrop of Operation Atlantic, which successfully froze approximately $12 million from a cybercriminal operation targeting crypto and investment fraudsters who used a technique known as “authorization phishing” to access crypto wallets and empty their funds.
Authorization phishing refers to a form of cryptocurrency fraud in which victims are tricked into signing blockchain transactions, giving the fraudster full control of their wallet and draining all their assets. According to TRM Labs, these phishing attacks are “often wrapped in investment or romance scams.”
“This tactic is commonly used in online investment scams called pig butchering to lure victims into handing over increasing amounts of money to scammers,” the U.S. Secret Service said in a statement.
More than 20,000 victims have been identified in 30 countries, including Canada and the United Kingdom, and U.S. authorities also seized more than 120 domains used by the attackers behind the phishing scheme and identified an additional $33 million in funds believed to be connected to the investment fraud scheme around the world.
In early April, the Treasury Department’s Office of Cybersecurity and Critical Infrastructure Protection (OCCIP) announced a new information-sharing initiative to strengthen cybersecurity across the digital asset industry. As part of this initiative, U.S. digital asset companies and industry organizations that meet Treasury Department standards will be eligible to receive actionable cybersecurity information at no additional cost.
“This initiative will provide eligible U.S. digital asset companies and industry organizations with timely, actionable cybersecurity information to help them better identify, prevent, and respond to cyber threats targeting their customers and networks,” the Treasury Department said.
Source link