Threat actors are actively exploiting a critical security flaw affecting the open-source content management system (CMS) known as MetInfo, according to new findings from VulnCheck.
The vulnerability in question is CVE-2026-29014 (CVSS score: 9.8), which is a code injection flaw that could lead to arbitrary code execution.
The NIST National Vulnerability Database (NVD) states, “MetInfo CMS versions 7.9, 8.0, and 8.1 contain an unauthenticated PHP code injection vulnerability that could allow a remote attacker to execute arbitrary code by sending a crafted request containing malicious PHP code.”
“An attacker could exploit insufficient input neutralization in the execution path to remotely execute code and gain complete control of an affected server.”
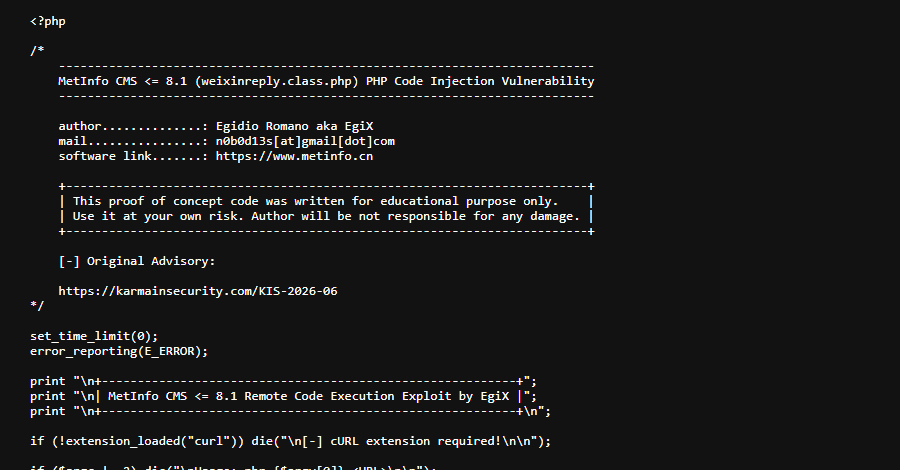
According to security researcher Egidio Romano, who discovered the vulnerability, the issue is due to the /app/system/weixin/include/class/weixinreply.class.php script not properly sanitizing the input provided by the user when making Weixin (also known as WeChat) API requests.
As a result, a remote unauthenticated attacker could exploit this loophole to inject and execute arbitrary PHP code. One of the key prerequisites for a successful exploit when MetInfo is running on a non-Windows server is that the “/cache/weixin/” directory must already exist. This directory is created when installing and configuring the official WeChat plugin.
A patch for CVE-2026-29014 was released by MetInfo on April 7, 2026. The vulnerability has been exploited as of April 25, with “a small number of exploits” deployed against susceptible honeypots in the United States and Singapore.
These efforts were initially sparse and related to automated probes, but activity spiked on May 1, 2026, with a focus on IP addresses in China and Hong Kong, said Caitlin Condon, vice president of security research at VulnCheck. As many as 2,000 MetInfo CMS instances are accessible online, most of them located in China.
Source link