Microsoft has revealed details of a large-scale credential theft campaign that combines decoy-themed code with legitimate email services to lure users to attacker-controlled domains and steal authentication tokens.
This multi-stage campaign, observed from April 14th to 16th, 2026, targeted over 35,000 users in over 13,000 organizations across 26 countries, with 92% of targets located in the United States. The majority of phishing emails were directed to the healthcare and life sciences (19%), financial services (18%), professional services (11%), and technology and software (11%) sectors.
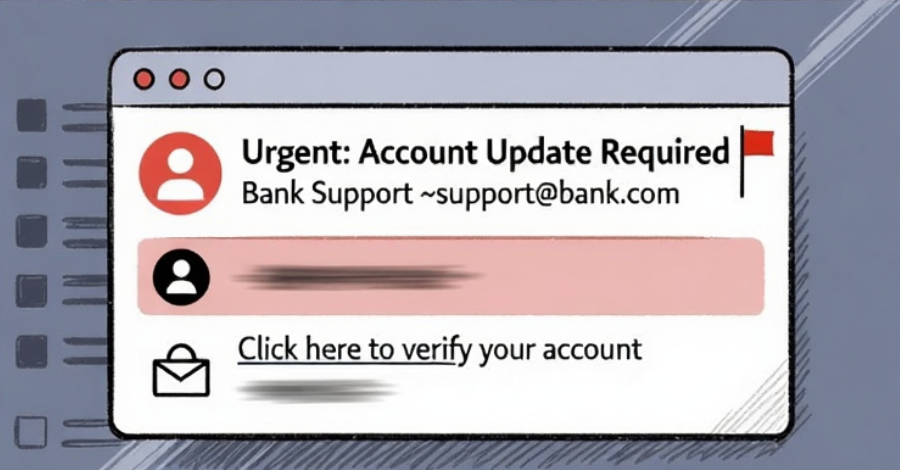
The Microsoft Defender Security Research Team and Microsoft Threat Intelligence said, “The campaign’s lures used sophisticated, enterprise-style HTML templates with structured layouts and pre-emptive authentication statements, making them appear more trustworthy than typical phishing emails and increasing their credibility as legitimate internal communications.”
“The campaign created a sense of urgency and pressure to take action, as the messages included repeated accusations and time-bound calls to action.”
Email messages used in this campaign use decoys related to code of conduct reviews, using display names such as “Internal Regulation COC,” “Employee Communications,” and “Team Conduct Report.” Subject lines for these emails include “Internal Incident Record Published Under Policy of Conduct” or “Reminder: Employer Has Published a Non-Compliant Incident Record.”
“The beginning of each message stated that the message was ‘published through an approved internal channel’ and that the links and attachments had been ‘reviewed and approved for secure access,’ supporting the email’s legitimacy,” Microsoft said.
The email will be evaluated as coming from a legitimate email delivery service. The message also includes a PDF attachment that purports to provide additional information regarding the conduct review, inviting victims to click on a link within the document to begin the credential collection flow.
This attack chain was found to lure victims through multiple CAPTCHAs and intermediary pages designed to disguise the scheme’s legitimacy while simultaneously thwarting automated defenses.

The end result is a sign-in experience that leverages Adversary-in-the-middle (AiTM) phishing tactics to collect Microsoft credentials and tokens in real-time, effectively allowing attackers to bypass multi-factor authentication (MFA). According to Microsoft, the final destination depends on whether the malicious flow was triggered from a mobile device or a desktop system.
Phishing trends in 2026
The disclosure comes as Microsoft’s analysis of the email threat landscape from January to March 2026 reveals that QR code phishing has emerged as the fastest growing attack vector and CAPTCHA gate phishing is evolving “rapidly” across payload types. The technology giant announced that it has detected approximately 8.3 billion total email-based phishing threats.
Of these, nearly 80% were link-based, with large HTML and ZIP files making up the majority of malicious payloads distributed via phishing emails. The end goal of the majority of these attacks was credential harvesting, and malware delivery dropped to just 5-6% by the end of the quarter.
Microsoft also said the operator of the Tycoon 2FA phishing-as-a-service (PhaaS) platform attempted to change its hosting provider and domain registration patterns following a coordinated sabotage operation in March 2026.
“Towards the end of March, we learned that Tycoon 2FA moved away from Cloudflare as a hosting service and is now hosting most of its domains on various alternative platforms. This suggests that the group is looking to find alternative services that offer comparable anti-analysis protection,” it added.

In a report published in February, Palo Alto Networks Unit 42 highlighted that attackers are abusing QR codes as URL shorteners to disguise malicious destinations, steal account credentials using in-app deep links, and bypass app store security by linking to direct downloads of malicious apps.
According to Microsoft data, QR code phishing has increased significantly over the last three months, with attack volume jumping from 7.6 million in January to 18.7 million in March, an increase of 146%. One notable development observed in late March was the use of QR codes embedded directly in the email body.
Business email compromise (BEC) fraud, on the other hand, showed greater volatility, with attack volume exceeding 4 million in March 2026, up from over 3.5 million in January and over 3 million in February. In total, 10.7 million BEC attacks were recorded.
Two notable campaigns observed in Q1 2026 are: –
Large-scale ongoing campaign from February 23 to February 25, 2026. Send over 1.2 million messages to users in over 53,000 organizations in 23 countries using 401(k), payments, and invoice-themed lures with SVG attachments. Upon opening the file, victims are directed to a CAPTCHA check, and upon successful completion, they are presented with a fake sign-in page to compromise their account. In a massive campaign that took place on March 17, 2026, more than 1.5 million verified malicious messages were sent to more than 179,000 organizations in 43 countries. This activity accounted for 7% of all malicious HTML attachments observed during the month. Upon opening this HTML file, victims are redirected to an initial phishing page where they are screened before directing the visitor to their final destination. The phishing page presented a CAPTCHA challenge before serving a fraudulent sign-in page.
“Interestingly, although the messages in this campaign shared common tooling, structure, and delivery characteristics, the infrastructure hosting the final phishing payload was linked to multiple different PhaaS providers,” Microsoft said. “While most of the phishing endpoints observed were related to Tycoon 2FA, other activity was related to Kratos (formerly Sneaky 2FA) and EvilTokens infrastructure.”
This finding is consistent with the emergence of phishing and BEC campaigns that exploit Amazon Simple Email Service (SES) as a delivery vector to bypass SPF, DKIM, and DMARC checks and facilitate credential theft via fake sign-in pages. These attacks often work by gaining access to Amazon SES through compromised AWS access keys.
“The insidious nature of the Amazon SES attack lies in the fact that the attackers are not using questionable or dangerous domains, but rather an infrastructure that both users and security systems have come to trust,” Kaspersky said.
“By weaponizing this service, attackers avoid the hassle of building questionable domains and email infrastructure from scratch. Instead, they gain the ability to hijack existing access keys and send out thousands of phishing emails at once. These messages pass email authentication, originate from IP addresses that are unlikely to be blocklisted, and contain links to phishing forms that look completely legitimate.”
Source link