A China-based cybercrime group known as Silver Fox is said to be involved in a new campaign targeting organizations in Russia and India using a new malware called ABCDoor.
The campaign used a phishing email mimicking a communication from India’s Income Tax Department in December 2025, followed by a similar campaign targeting Russian companies.
“Both waves followed almost the same structure: the phishing emails either masqueraded as official notifications about tax audits or urged users to download archives containing ‘lists of tax violations,'” Kaspersky said. “Inside the archive was a modified Rust-based loader obtained from a public repository that downloads and executes the well-known ValleyRAT backdoor.”
The campaign is estimated to have impacted organizations across industrial, consulting, retail, and transportation sectors. More than 1,600 phishing emails were reported between early January and early February.
Notable in these waves of phishing is the delivery of a new ValleyRAT plugin that acts as a loader for a previously undocumented Python-based backdoor (codenamed ABCDoor). The backdoor has been part of the attackers’ arsenal since at least December 19, 2024, and has been used in cyberattacks since February or March 2025, the Russian cybersecurity firm said.
The starting point of the attack chain is a phishing email containing a PDF file. This file contains two clickable links that lead to downloading a ZIP or RAR archive hosted at ‘abc.haijing88’.[.]com.” The campaign, detected in December 2025, allegedly embedded malicious code directly within files attached to emails.
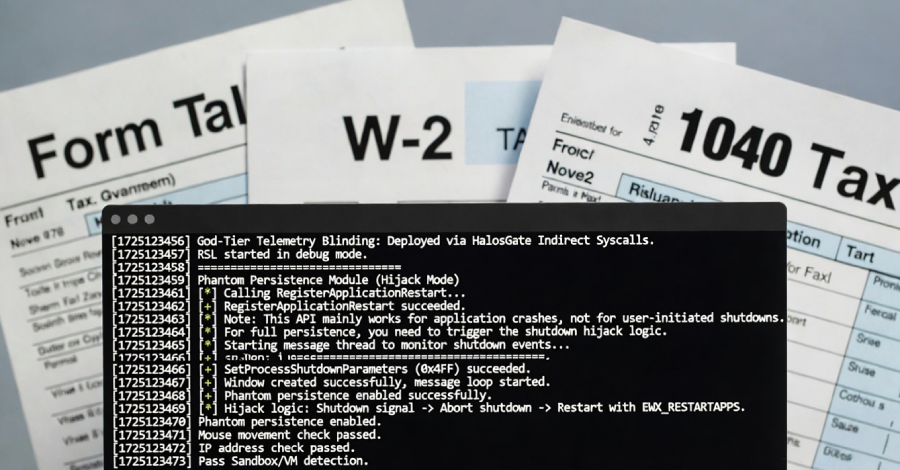
Inside the archive is an executable file that mimics a PDF file. This binary is a modified version of an open-source shellcode loader and antivirus bypass framework called RustSL. Silver Fox’s first recorded use of RustSL dates back to late December 2025.
The ultimate goal of the Silver Fox RustSL variant is to implement country-based geofencing and environment checks to detect virtual machines and sandboxes while unpacking encrypted malicious payloads. The GitHub variant only includes China in its list of countries, while the bespoke version includes India, Indonesia, South Africa, Russia, and Cambodia.
One of the loader variants was found to use a new technique called Phantom Persistence to establish persistence on compromised hosts. It was first documented in June 2025.

“This method exploits a feature designed to allow applications that require a restart for updates to properly complete the installation process,” Kaspersky explained. “The attacker intercepts the system’s shutdown signal, halts the normal shutdown sequence, and triggers a reboot under the guise of a malware update, which the loader then forces the system to run upon OS startup.”
The encrypted payload loaded by RustSL downloads the encrypted ValleyRAT (aka Winos 4.0) malware, and the core component (‘login-module.dll_bin’) is responsible for command and control (C2) communication, command execution, and retrieval and execution of additional modules.
One of the custom modules introduced as part of the second geofencing post-check attack is ABCDoor. ABCDoor connects to external servers over HTTPS, processes incoming messages and facilitates persistence, handles backdoor updates and deletions, collects data such as screenshots, enables remote mouse and keyboard control, performs file system operations, manages system processes, and leaks clipboard contents.
As recently as November 2025, Silver Fox was observed using a JavaScript loader to deliver ABCDoor, possibly via a self-extracting (SFX) archive packaged within a ZIP archive sent via a phishing email. Since then, new versions of RustSL have expanded its coverage to include Japan.
The most attacks were detected in India, Russia, and Indonesia, followed by South Africa and Japan. The majority of loader samples discovered used tax-themed lures to mimic infection sequences.
“After 2024, [Silver Fox] “The group has evolved into a dual-track operational model that involves large-scale, highly profitable opportunistic and espionage operations at the same time. Initially, the group targeted China, but has since expanded its scope of operations to Taiwan and Japan,” S2W said.
“Silver Fox Group primarily utilizes highly customized spear phishing techniques for initial entry, deploying sophisticated and diverse attack scenarios tailored to the seasonal issues of the target country and the nature of the target’s job.”
Source link