A “novel” social engineering campaign that leverages the cross-platform note-taking application Obsidian as an initial access vector to distribute a previously undocumented Windows remote access Trojan called PHANTOMPULSE has been observed in attacks targeting individuals in the financial and cryptocurrency sectors.
The campaign, named REF6598 by Elastic Security Labs, was found to utilize sophisticated social engineering tactics to infiltrate both Windows and macOS systems via LinkedIn and Telegram, approaching prospective individuals posing as a venture capital firm, and then moving the conversation to a Telegram group with multiple purported partners.
Telegram’s group chat is designed to give this operation a bit of credibility, with members discussing topics related to financial services and crypto liquidity solutions. The target is then instructed to use Obsidian to connect to a container hosted in the cloud using the provided credentials and access what appears to be a shared dashboard.
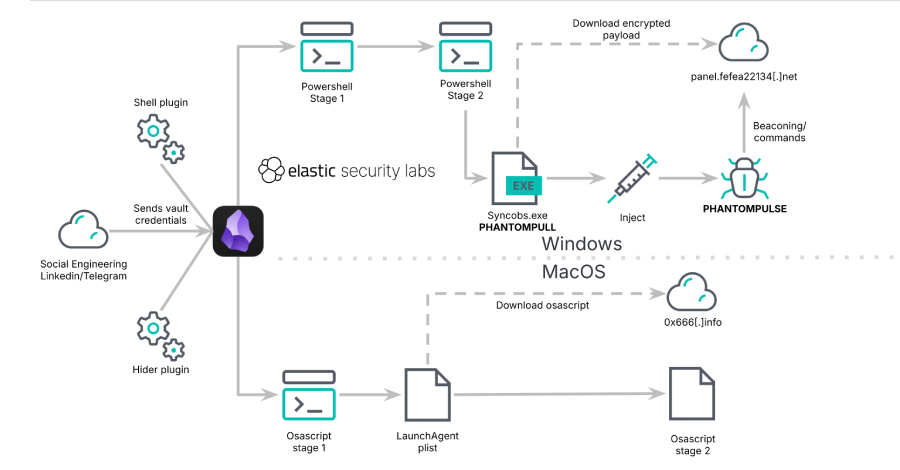
It is this vault that triggers the infection sequence. As soon as the vault is opened in a note-taking application, the target is asked to enable syncing of “installed community plugins”, effectively executing malicious code.
“The attackers exploit Obsidian’s legitimate community plugin ecosystem, specifically the Shell Commands and Hider plugins, to silently execute code when victims open a shared cloud vault,” researchers Salim Bitam, Samir Bousseaden and Daniel Stepanic said in a technical breakdown of the campaign.
Given that this option is disabled by default and cannot be turned on remotely, the attacker would need to convince the target to manually toggle community plugin sync on the device so that the malicious vault configuration can trigger command execution via the shell command plugin. Also used in conjunction with Shell Commands is another plugin named Hider for hiding certain user interface elements in Obsidian, such as the status bar, scrollbars, and tooltips.
“Although this attack requires social engineering to cross the synchronization boundaries of a community plugin, this technique remains noteworthy. It exploits legitimate application functionality as a persistence and command execution channel, the payload resides entirely within a JSON configuration file, and is unlikely to trigger traditional AV.” [antivirus] “Parent process-based detection is an important layer because it is signed and execution is handed off by a signed and trusted Electron application,” the researchers said.
Depending on the operating system, dedicated execution paths are activated. On Windows, this command calls a PowerShell script that drops an intermediate loader code-named PHANTOMPULL that decrypts the PHANTOMPULSE and launches it in memory.
PHANTOMPULSE is an artificial intelligence (AI) generated backdoor that uses the Ethereum blockchain to resolve command and control (C2) servers by retrieving the latest transactions associated with hard-coded wallet addresses. Once a C2 address is obtained, the malware uses WinHTTP for communication, allowing it to send system telemetry data, fetch and execute commands, upload files or screenshots, and capture keystrokes.
The supported commands are designed to facilitate comprehensive remote access.
inject, inject shellcode/DLL/EXE into target process Drop, drop file to disk and perform screenshot, capture and upload screenshot keylog, start/stop keylogger uninstallation, initiate persistence removal, perform cleanup Elevate, elevate privileges to SYSTEM via COM elevation moniker downgrade, migrate from SYSTEM to elevated administrator
On macOS, the Shell Commands plugin provides an obfuscated AppleScript dropper that iterates over a hardcoded list of domains while using Telegram as a dead drop resolver for fallback C2 resolution. This approach allows for easy rotation of the C2 infrastructure, increasing flexibility and making domain-based blocking insufficient.
In the final step, the dropper script connects to the C2 domain, downloads and executes the second stage payload via osascript. The exact nature of this payload remains unknown, given that the C2 server is currently offline. The infiltration ultimately failed as the attack was detected and blocked before the attacker could accomplish their goal on the infected machine.
“REF6598 demonstrates how threat actors continue to find creative initial access vectors by exploiting trusted applications and utilizing targeted social engineering,” Elastic said. “Rather than exploiting software vulnerabilities, by exploiting Obsidian’s community plugin ecosystem, attackers completely bypass traditional security controls and rely on an application’s intended functionality to execute arbitrary code.”
Source link