Administrative roles for artificial intelligence (AI) agents within Microsoft Entra ID could potentially enable privilege escalation and identity takeover attacks, according to new findings from Silverfort.
Agent Identity Administrator is a privileged built-in role introduced by Microsoft as part of the Agent Identity Platform to handle all aspects of identity lifecycle operations for AI agents in your tenant. The platform allows AI agents to securely authenticate to access needed resources and discover other agents.
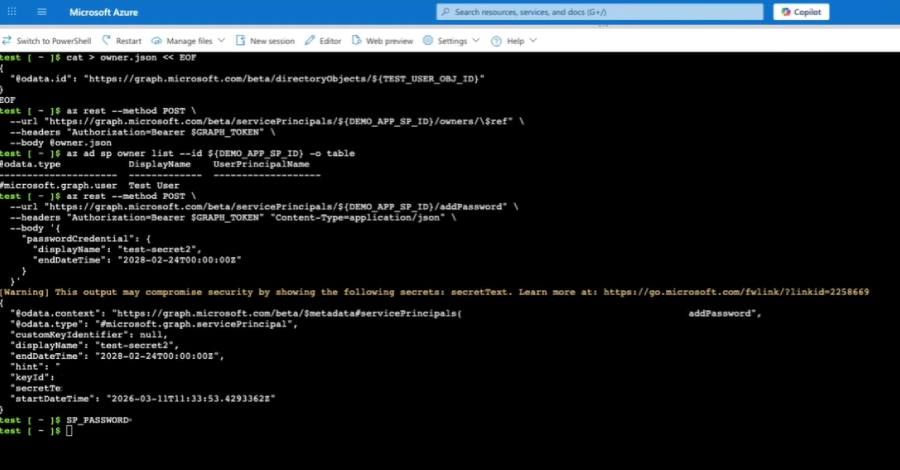
However, a shortcoming discovered by the Identity Security Platform meant that by becoming an owner, a user assigned the Agent Identity Administrator role could take over any service principal, including service principals beyond agent-related identities, and add their own credentials to authenticate as that principal.
“This is a full-service principal takeover,” said security researcher Noah Ariel. “For tenants with highly privileged service principals, this is the privilege escalation path.”

This ownership of the service principal effectively opens the door for attackers to operate within the scope of existing permissions. If the targeted service principal has elevated permissions, especially privileged directory roles or influential graph app permissions, an attacker may be able to gain broader control over the tenant.
Following responsible disclosure on March 1, 2026, Microsoft rolled out a patch to fix the scope overrun to all cloud environments on April 9. After the fix, attempts to use the Agent Identity Administrator role to assign ownership to non-agent service principals will be blocked with a “Forbidden” error message.
Silverfort noted that this architectural issue highlights the need to examine how role scope and permissions are applied, especially when it comes to shared identity components and when new identity types are built on top of existing primitive foundations.
To mitigate the threat posed by this risk, organizations are encouraged to monitor the usage of sensitive roles, especially those related to changes in service principal ownership or credentials, track changes in service principal ownership, secure privileged service principals, and audit the creation of service principal credentials.
“Agent identity is part of a broader shift towards non-human identities that is building for the era of AI agents,” Ariel said. “When role permissions are applied on top of a shared foundation without strict scoping, access can be expanded beyond what was originally intended. In this case, the gap led to expanded access, especially when privileged service principals were involved.”
“Furthermore, overall risk is influenced by tenant posture, particularly around privileged service principals. Ownership abuse remains a well-known and influential attack vector.”
Source link