NASA’s Office of Inspector General (OIG) has revealed how Chinese nationals posed as U.S. researchers as part of a spear-phishing campaign to obtain sensitive information from space agencies, government agencies, universities, and private companies in violation of export control laws.
“For years, NASA employees and research collaborators believed they were simply sharing software with their colleagues,” the OIG said in a release Thursday. “Instead, they were emailing sensitive defense technology to Chinese people pretending to be U.S. engineers.”
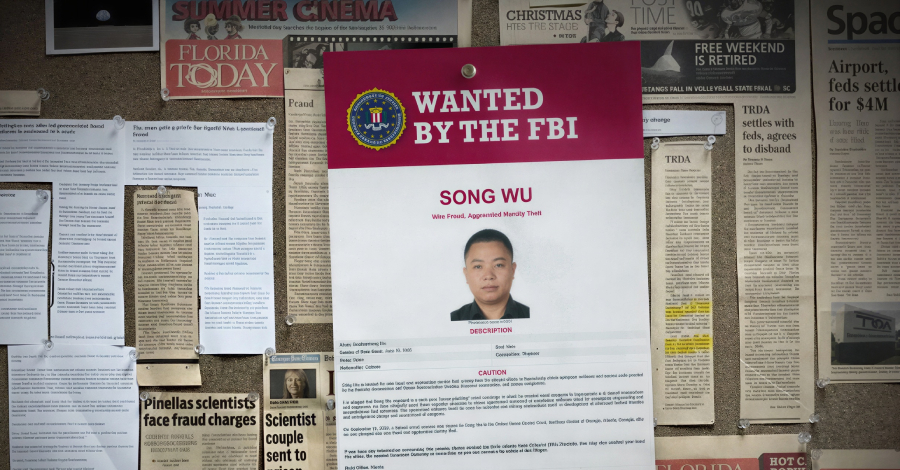
It was revealed in September 2024 that the person involved in this campaign was Chinese national Song Wu, and the US Department of Justice (DoJ) announced charges against him for orchestrating a multi-year campaign that ran from January 2017 to December 2021 and targeted dozens of US professors, researchers, and engineers.
Some of the campaign’s victims were employed by NASA, the Air Force, Navy, Army, and Federal Aviation Administration, as well as major universities and private companies.
According to the 2024 indictment, Song was an engineer at Aviation Industry Corporation of China (AVIC), a Chinese state-owned aerospace and defense conglomerate founded in 2008. In an effort to obtain modeling software used in aerospace design and weapons development, Song and his co-conspirators allegedly posed as friends and colleagues, gained access to proprietary software and source code, and conducted extensive research on their targets.
OIG said the scheme was successful in a small number of cases where victims shared sensitive information with fake accounts controlled by Song and others without realizing they were violating U.S. export control laws.
Mr. Song is charged with wire fraud and 14 counts of aggravated identity theft, each of which could carry a maximum sentence of 20 years in prison. If convicted of aggravated identity theft, he could be sentenced to two consecutive years in prison. The 40-year-old man remains at large.
Adding Song to the US’s most wanted list, the US Federal Bureau of Investigation (FBI) said the specialized software could be used for industrial and military applications, including the development of advanced tactical missiles and the aerodynamic design and evaluation of weapons.
“As phishing operations become increasingly sophisticated, there are common clues that can betray fraudsters and uncover export fraud schemes,” the OIG said. “In Mr. Song’s case, he requested the same software multiple times without justifying why he needed it.”
“Export control fraudsters also often offer unusual payment methods (such as suspicious wire transfers), abruptly change payment terms or payment sources, or use unusual transfer methods to hide their identity and circumvent shipping restrictions.”
Source link